IEC 62443 Compliance with Complyan
Welcome to the world of industrial cybersecurity! In the era of Industry 4.0, automation and connectivity have become the norm, and with it, robust cybersecurity measures are needed.
The International Electrotechnical Commission (IEC) has developed a series of standards under the IEC 62443 Framework to address the unique cybersecurity challenges facing industrial control systems (ICS). This series of standards provides guidance on establishing, implementing, and maintaining cybersecurity measures for industrial automation and control systems (IACS).
The IEC 62443 framework consists of several sub-frameworks, each focusing on different aspects of industrial cybersecurity, including network security, system security, and product security. These sub-frameworks provide a holistic approach to cybersecurity, covering all product lifecycle stages, from design to decommissioning.
In this article, we will closely examine the IEC 62443 framework and explore its different sub-frameworks. We will discuss how this framework can help organizations ensure the security and integrity of their industrial control systems and how Complyan can assist with implementing and maintaining compliance with this important cybersecurity framework.
Understanding The IEC 62443
Sub-frameworks
The IEC 62443 framework has many sub-frameworks that focus on different aspects of industrial cybersecurity. Some of the sub-frameworks in the series include:
- General concepts and models in IEC 62443-1-x – This framework outlines essential terms and concepts relevant to industrial cybersecurity and gives an overview of the IEC 62443 family of standards.
- Policies and procedures – IEC 62443-2-x – This framework focuses on creating policies and practices that enable industrial cybersecurity to bloom in organizations with Industrial control systems.
- System security criteria and security levels – IEC 62443-3-x – This framework offers instructions on how to recognize and evaluate security threats, as well as create security standards for industrial control systems.
- Secure Product Development Lifecycle – IEC 62443-4-x – This framework offers instructions on including cybersecurity into the industrial control system product development lifecycle.
- Secure system integration – IEC 62443-5-x – The secure integration of industrial control systems into more complex systems and networks is the main objective of this framework.
- Security for Industrial Automation and Control Systems (IACS): IEC 62443-6-x This framework offers instructions on how to put cybersecurity precautions for IACS into practice.
- Technical security criteria for IACS components, IEC 62443-7-x – For specific IACS components, this framework offers in-depth technical assistance in implementing security measures.
Security Levels
The five Security Levels of IEC 62443 are as follows:
- Security Level 0
This level has no specific requirements or security protection necessary. - Security Level 1
At this level, the system needs protection against casual or coincidental violations. - Security Level 2
This level requires protection against intentional violation using simple means. These means involve low resources, generic skills, and low motivation. - Security Level 3
At this level, the system needs protection against intentional violation using sophisticated means. These means involve moderate resources, IACS-specific skills, and moderate motivation. - Security Level 4
This level requires protection against intentional attacks with sophisticated means. These means involve extended resources, IACS-specific skills, and high motivation.
Requirements
The IEC 62443 framework sets the standards for securing industrial automation and control systems (IACS). One of the key features of this framework is the seven foundational requirements that must be met for each security level (SL). These requirements serve as the backbone of the framework and help ensure that the IACS has the necessary security and safety safeguards in place.
Let’s take a closer look at each of these foundational requirements:
- Identification and Authentication Control: This requirement ensures that all users, whether humans, software processes, or devices, are reliably identified and authenticated before accessing the IACS. This helps prevent unauthorized access and ensures that only authorized personnel have access to critical systems and data.
- Use Control: The use control requirement enforces the assigned privileges of an authenticated user to perform requested actions on the system or assets. It also includes monitoring the use of these privileges, which helps detect any suspicious activity or misuse of privileges.
- System Integrity: This requirement ensures the integrity of the IACS and prevents unauthorized manipulation. It also includes measures to detect and respond to any changes to the system that may indicate a security breach.
- Data Confidentiality: This requirement ensures the confidentiality of information on communication channels and in data repositories. It includes measures to prevent unauthorized disclosure and protect sensitive information.
- Restricted Data Flow: This requirement segments the control system via zones and conduits to limit unnecessary data flow. This helps prevent unauthorized access to critical systems and data.
- Timely Response to Events: This requirement mandates a timely response to security violations. It also requires notifying the proper authorities and reporting necessary evidence of the violation. It also includes taking timely corrective action when incidents occur.
- Resource Availability: The final foundational requirement ensures the availability of the control system against the degradation or denial of essential services. This is critical in ensuring that the IACS can continue to operate even in the event of an attack or other security incident.
It’s important to note that each foundational requirement has multiple conditions that must be met depending on the Security Level. The higher the SL, the more conditions to be met for each foundational requirement. Meeting these requirements is crucial in ensuring the security and safety of industrial control systems, and the IEC 62443 framework provides a comprehensive guide to achieving this goal.
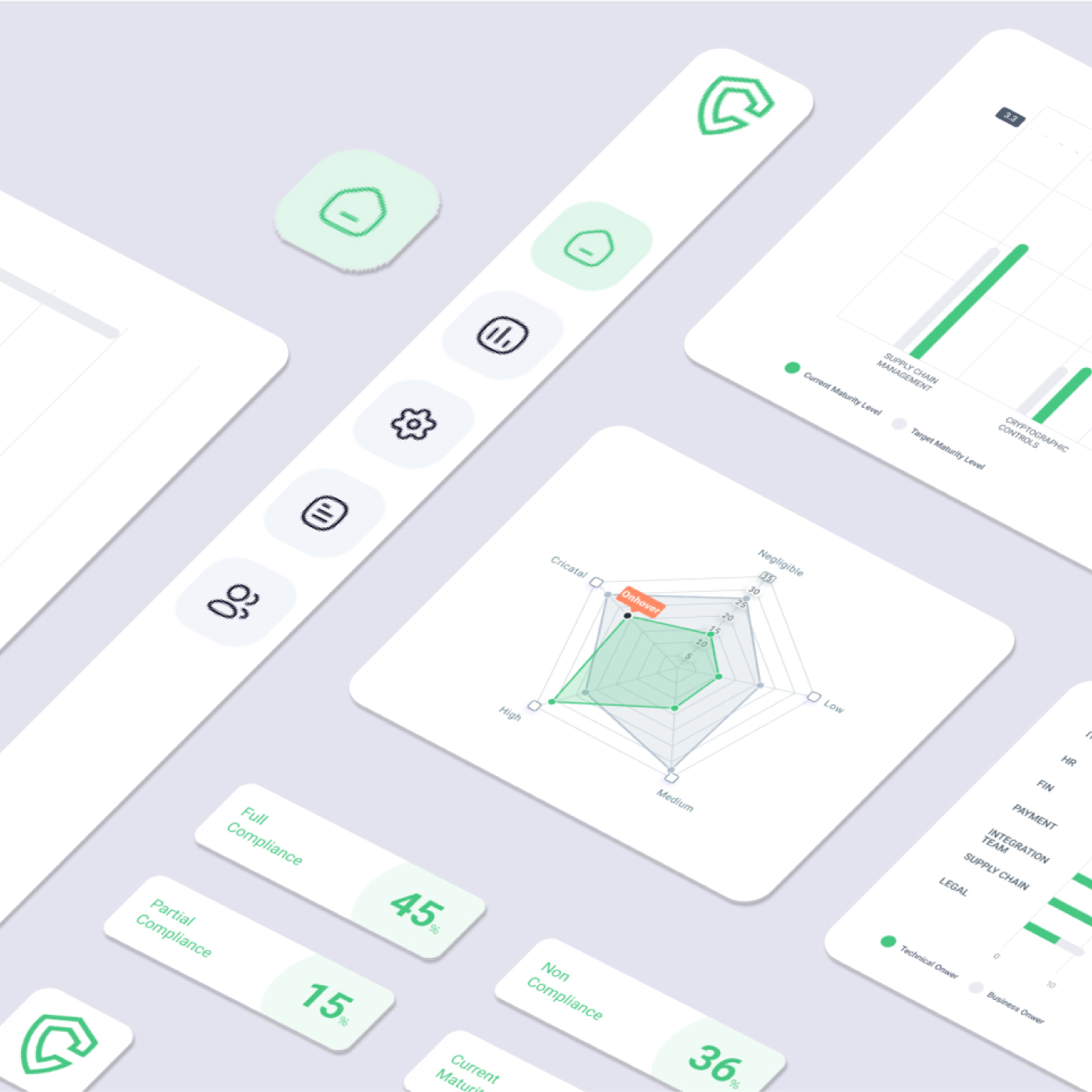
Mapping IEC 62443 Requirements to Complyan Modules
Complyan is an intuitive cybersecurity compliance automation platform that offers plug-and-play compliance management solutions. Complyan offers these solutions in modules to help organizations group, evaluate, and track their cybersecurity compliance efforts. This SaaS solution can help streamline compliance with the IEC 62443 framework in the following ways:
- Identification and Authentication Control
The Data Security and Privacy Module can help achieve compliance with this requirement by providing tools to manage user access and credentials. The module includes features such as multi-factor authentication and user access management to reliably identify and authenticate all users attempting to access the ICS. - Use Control
The Cyber Risk Management Module can help achieve compliance with this requirement by providing tools to enforce user privileges and monitor their actions. The module includes features such as user activity monitoring and automated access control to ensure that only authorized users have access to the system and its assets. - System Integrity
The Cyber Risk Management Module can help achieve compliance with this requirement by providing tools to monitor the IACS for unauthorized changes or manipulation. The module includes features such as change management and configuration tracking to ensure that the system remains intact and any changes are authorized and documented. - Data Confidentiality
The Data Security and Privacy Module can help achieve compliance with this requirement by providing tools to secure data both in transit and at rest. The module includes features such as encryption and data masking to ensure that information is kept confidential and to prevent unauthorized disclosure. - Restricted Data Flow
The Third-Party Risk Management Module can help achieve compliance with this requirement by providing tools to manage and segment the control system through zones and conduits. The module includes features such as supply chain risk management and access control to limit the flow of data and prevent unnecessary access to critical assets. - Timely Response to Events
The Cyber Risk Management Module can help achieve compliance with this requirement by providing tools to detect and respond to security violations. The module includes features such as incident response planning and automated threat detection to ensure that security incidents are addressed promptly and effectively. - Resource Availability
The Information Security Policy Builder Module can help achieve compliance with this requirement by providing tools to develop and implement policies and procedures to ensure the availability of the control system. The module includes risk assessment and business continuity planning to help prevent the degradation or denial of essential services.




 Governance and Policy Management
Governance and Policy Management