SOC 2 Compliance Framework: Building Trust Through Security Excellence

Modern businesses face mounting pressure to demonstrate their commitment to data protection and security controls. Customers demand transparency about how their sensitive information is handled, stored, and protected. SOC 2 compliance has emerged as the gold standard for organizations seeking to validate their security posture and earn customer confidence.
What is the SOC 2 Framework?
The System and Organization Controls (SOC) 2 framework represents a comprehensive set of standards developed by the American Institute of Certified Public Accountants (AICPA). This voluntary compliance standard evaluates how service organizations manage customer data according to five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Unlike regulatory mandates, SOC 2 serves as a voluntary demonstration of an organization’s commitment to protecting customer data. The framework provides a structured approach to implementing, maintaining, and validating security controls that protect sensitive information throughout its lifecycle.
The Five Trust Services Criteria Explained
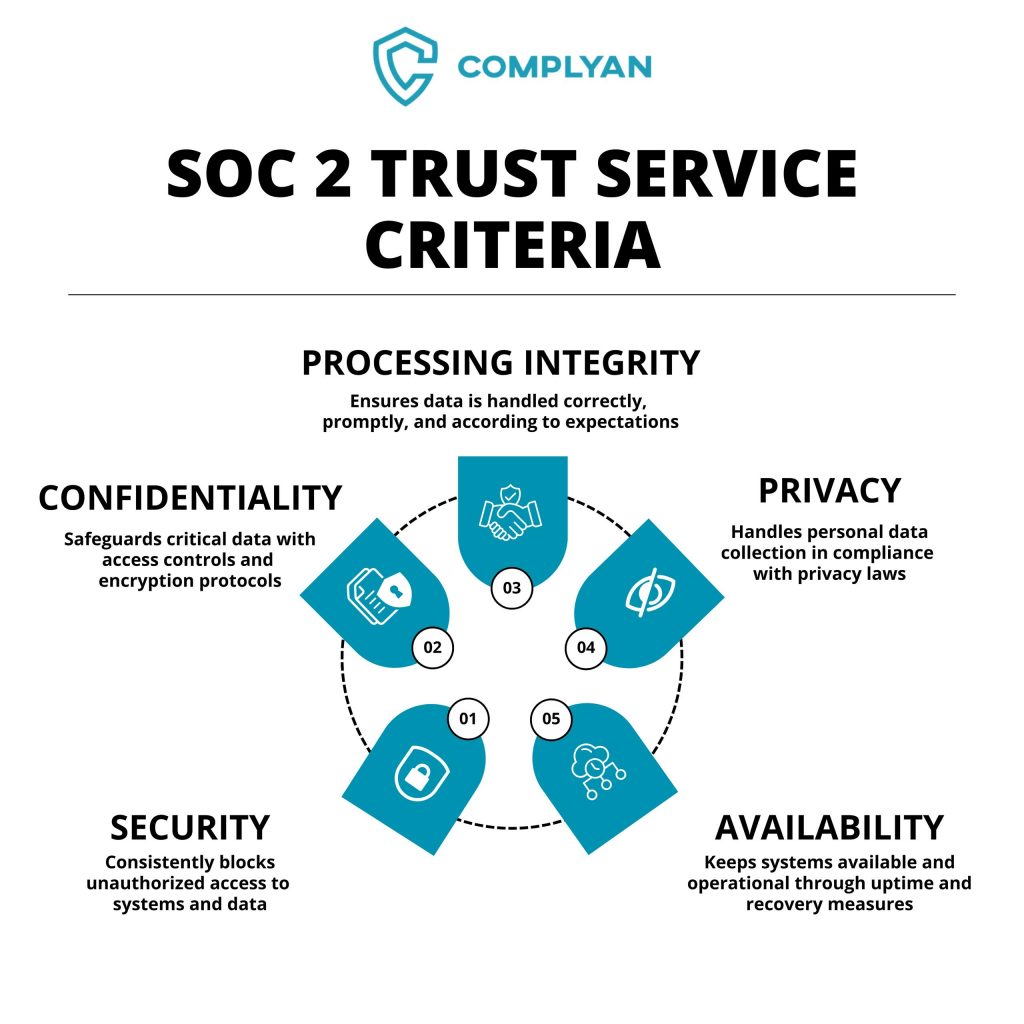
The AICPA has established five distinct Trust Services Criteria that form the backbone of SOC 2 compliance. Each criterion addresses specific aspects of data protection and system reliability, creating a comprehensive framework for organizational security assessment.
Security forms the foundation of every SOC 2 audit and must be included in all assessments. This criterion encompasses access controls, network security, system monitoring, and incident response procedures. Organizations must demonstrate robust protection against unauthorized access, data breaches, and security incidents through technical safeguards, administrative controls, and physical security measures.
Availability focuses on system accessibility and uptime commitments. This criterion becomes essential for organizations providing critical services where downtime directly impacts customer operations. It includes disaster recovery planning, system monitoring, capacity management, and business continuity procedures that ensure consistent service delivery.
Processing Integrity addresses the accuracy, completeness, and timeliness of data processing. Organizations handling financial transactions, payroll processing, or other critical data operations typically include this criterion to demonstrate reliable system performance and data accuracy throughout processing workflows.
Confidentiality protects information designated as confidential through contractual agreements or business requirements. This criterion extends beyond public information to cover proprietary data, trade secrets, intellectual property, and other sensitive business information requiring enhanced protection measures.
Privacy specifically addresses the protection of personally identifiable information (PII). Organizations collecting, storing, or processing personal data must demonstrate comprehensive privacy controls including data minimization, consent management, breach notification procedures, and compliance with applicable privacy regulations.
SOC 2 Type I vs. Type II Reports
Understanding the distinction between Type I and Type II reports is crucial for determining the appropriate compliance path for your organization.
A Type I report provides a point-in-time assessment of control design and implementation. This snapshot approach validates that appropriate controls exist but doesn’t evaluate their operational effectiveness over time. Type I reports typically serve as stepping stones toward full compliance or interim measures while preparing for Type II audits.
A Type II report examines control effectiveness over a specified period, typically ranging from three to twelve months. This comprehensive assessment demonstrates sustained operational excellence and provides stronger assurance to customers and stakeholders. Most enterprise customers prefer Type II reports due to their thorough evaluation of long-term control effectiveness.
Who Benefits from SOC 2 Compliance?
SOC 2 compliance particularly benefits organizations that store, process, or transmit customer data through cloud-based services. Software-as-a-Service (SaaS) providers, cloud hosting companies, managed service providers, and data centers frequently pursue SOC 2 compliance to meet customer requirements and competitive demands.
The framework proves especially valuable for B2B organizations seeking enterprise customers. Large organizations typically include SOC 2 compliance as a prerequisite in their vendor assessment processes, making compliance essential for accessing lucrative enterprise markets.
For businesses operating in the SaaS ecosystem, Cybersecurity GRC platforms like Complyan can significantly streamline the path to SOC 2 certification. These platforms automate evidence collection, control monitoring, and compliance reporting, reducing the manual effort traditionally required for maintaining compliance posture.
The SOC 2 Compliance Process
1. Scope Definition and Planning
The compliance journey begins with determining applicable Trust Services Criteria based on your business model, customer requirements, and data handling practices. Most organizations start with Security and Availability, adding additional criteria based on specific business needs.
Proper scoping considers your entire technology stack, business processes, and organizational structure. This includes identifying systems, applications, data flows, and personnel that fall within the audit boundary.
2. Risk Assessment and Gap Analysis
Comprehensive risk assessment identifies vulnerabilities and control deficiencies across your organization. This process examines current policies, procedures, technical controls, and organizational practices against SOC 2 requirements.
Gap analysis reveals specific areas requiring remediation and helps prioritize implementation efforts. Organizations often discover significant gaps in documentation, access controls, monitoring procedures, and incident response capabilities.
3. Control Implementation and Documentation
Implementing required controls involves establishing formal policies, deploying technical safeguards, and creating operational procedures. This phase typically requires significant coordination across IT, security, human resources, and management teams.
Documentation plays a critical role in demonstrating control effectiveness. Organizations must maintain comprehensive records of policy implementation, control testing, incident management, and ongoing monitoring activities.
4. Continuous Monitoring and Evidence Collection
SOC 2 compliance requires ongoing demonstration of control effectiveness through systematic evidence collection. This includes log reviews, access control reports, security training records, vulnerability scan results, and incident response documentation.
Automated GRC platforms provide significant advantages in this phase by continuously collecting evidence, monitoring control effectiveness, and generating compliance reports. Modern compliance automation solutions can integrate with existing security tools, cloud infrastructure, and business applications to automatically gather required evidence without manual intervention.
Regular testing and validation ensure controls remain effective as business operations expand and change. Organizations benefit from real-time compliance dashboards that provide visibility into control status and identify areas requiring attention.
5. External Audit Process
Independent Certified Public Accountants (CPAs) conduct SOC 2 audits according to strict AICPA standards. The audit process involves control testing, evidence review, and validation of operational effectiveness throughout the specified period.
Auditors examine policies, interview personnel, review technical configurations, and validate evidence supporting control implementation. The final report provides detailed findings and opinions regarding control design and operational effectiveness.
Business Benefits of SOC 2 Compliance
SOC 2 compliance delivers tangible business value beyond regulatory requirements. Organizations typically experience accelerated sales cycles, improved customer trust, and enhanced competitive positioning.
Revenue Growth: Enterprise customers increasingly require SOC 2 compliance before engaging with service providers. Compliance removes barriers to enterprise sales and enables access to larger contract opportunities.
Risk Mitigation: Implementing SOC 2 controls significantly reduces security risk exposure and potential breach impacts. Organizations benefit from improved incident response capabilities, enhanced monitoring, and stronger access controls.
Operational Excellence: The compliance process often reveals opportunities for process improvement and operational efficiency gains. Organizations typically emerge with better documentation, clearer procedures, and stronger internal controls.
Competitive Advantage: SOC 2 compliance differentiates organizations in crowded markets and demonstrates commitment to security excellence. This credential becomes increasingly important as customers prioritize vendor security assessments.
Implementation Challenges and Solutions
Organizations frequently encounter common challenges during SOC 2 implementation including resource constraints, technical complexity, and documentation requirements. Success requires dedicated project management, cross-functional coordination, and sustained executive support.
Resource Allocation: SOC 2 implementation demands significant time investment from technical, security, and administrative personnel. Organizations should plan for 3-6 months of intensive preparation before initial audits.
Technical Implementation: Deploying required security controls often requires infrastructure changes, software configurations, and integration work. Organizations benefit from automated GRC solutions that simplify control implementation and evidence collection through native integrations with cloud platforms, security tools, and business applications.
Change Management: SOC 2 compliance affects daily operations and requires employee training, procedure updates, and cultural adaptation. Successful implementations emphasize communication, training, and gradual process adoption supported by automated workflows that reduce manual compliance tasks.
For organizations seeking expert guidance through the compliance process, automated cybersecurity GRC platforms like Complyan provide comprehensive support from initial assessment through ongoing maintenance, combining technology automation with compliance expertise.
Maintaining Ongoing Compliance
SOC 2 compliance represents an ongoing commitment rather than a one-time achievement. Organizations must maintain controls, collect evidence, and undergo annual audits to preserve their compliance status.
Annual Audit Requirements: SOC 2 reports remain valid for twelve months from issuance date. Organizations typically schedule annual audits to maintain current compliance status and meet customer expectations.
Continuous Improvement: Successful compliance programs emphasize continuous improvement through regular control assessments, process optimization, and technology updates. Organizations should treat SOC 2 as a foundation for broader security excellence.
Stakeholder Communication: Maintaining stakeholder confidence requires transparent communication about compliance status, control updates, and any identified issues. Organizations benefit from regular compliance reporting to customers and internal stakeholders.
Cost Considerations and Investment Planning
SOC 2 audit costs typically range from $15,000 to $75,000 depending on organizational complexity, selected criteria, and audit scope. Additional costs include control implementation, technology investments, and internal resource allocation.
Organizations should consider SOC 2 compliance as a strategic investment rather than a compliance expense. The revenue opportunities, risk reduction, and operational benefits typically justify the implementation costs within the first year.
Cost Optimization Strategies: Organizations can reduce compliance costs through automation, standardized processes, and efficient evidence collection. Investing in automated cybersecurity GRC platforms often provides significant long-term savings by reducing manual effort, minimizing audit preparation time, and maintaining continuous compliance readiness.
Future Outlook and Recommendations
SOC 2 compliance continues gaining importance as organizations increasingly rely on cloud services and data-driven business models. Customer expectations regarding vendor security assessments will likely become more stringent, making compliance essential for competitive success.
Organizations should approach SOC 2 compliance as part of a comprehensive security strategy rather than an isolated requirement. Building strong security foundations enables expansion into additional compliance frameworks and supports long-term business growth.
The investment in SOC 2 compliance pays dividends through enhanced customer trust, improved security posture, and access to enterprise market opportunities. Organizations that prioritize compliance early in their growth trajectory position themselves for sustained success in competitive markets.
Conclusion
SOC 2 compliance represents a critical milestone for organizations seeking to demonstrate security excellence and earn customer trust. While the implementation process requires significant investment and commitment, the business benefits justify the effort through enhanced competitive positioning, risk reduction, and revenue growth opportunities.
Success requires careful planning, comprehensive implementation, and ongoing commitment to security excellence. Organizations that treat SOC 2 as a strategic advantage rather than a compliance burden typically achieve better outcomes and stronger market positions.
The framework provides a structured approach to building robust security controls while meeting customer expectations for transparency and accountability. For organizations ready to invest in compliance excellence, SOC 2 offers a proven path to enhanced security posture and business success.




 Governance and Policy Management
Governance and Policy Management