Remote Work During Conflict: Maintaining Security and Compliance Beyond the Office

When conflict or sustained regional disruption forces organizations to move their workforce offsite, the first priority is almost always continuity. Security gets patched in later. Compliance follows after that, if at all. That sequencing is understandable. It is also dangerous.
The scale of what is at stake is no longer theoretical. In March 2026, the UAE Cybersecurity Council issued a formal advisory through the Emirates News Agency (WAM) confirming that remote-work-related cyber incidents have risen by more than 40 percent over recent years. The Council identified a direct and measurable link between the growth of remote work and a surge in attacks targeting home infrastructure, personal devices, and enterprise VPNs and it urged both organizations and individuals to treat remote work security as an active operational priority.
For any company that permits employees to work from home without a formal security plan, there are serious financial, legal, and regulatory ramifications. This is not merely an ambiguous threat.
The Numbers Behind the Risk
The UAE Cybersecurity Council’s data is specific: approximately 40 percent surge in current cyberattacks target remote work infrastructure home routers, personal devices, and VPNs, rather than hardened corporate systems. In 2025 alone, UAE authorities recorded over 12,000 Wi-Fi breaches, accounting for roughly 35 percent of all national cyber incidents that year
The global picture is consistent:
- 75% of IT professionals report their organizations are more exposed to cyber threats since switching to remote work 95% of cybersecurity breaches involve human error as a contributing factor
- During the COVID-19 pandemic, when remote work surged at scale, cyberattacks climbed by 630 percent globally
- 92% of cybersecurity experts believe remote and hybrid work models increase data breach risk, primarily due to reliance on unsecured home networks and personal devices
Compliance Obligations Do Not Pause During a Crisis
For organizations operating in or with the Middle East, the regulatory picture is specific and enforceable, not something that can be deferred until stability returns.
In the UAE, the Information Assurance Regulation (IAR), overseen by the Telecommunications and Digital Government Regulatory Authority (TDRA), comprises 188 security controls covering access management, incident response, endpoint security, and business continuity. It is mandatory for federal and local government entities, critical infrastructure operators, and private sector organizations handling national-level data. Non-compliance carries penalties of up to $5 million, potential criminal charges, and license suspension.
In Saudi Arabia, the National Cybersecurity Authority (NCA) governs compliance through its Essential Cybersecurity Controls (ECC) and the dedicated Telework Cybersecurity Controls (TCC-1:2021) 21 controls and 42 sub-controls built specifically to secure remote work operations, covering VPN access, multi-factor authentication, endpoint security, and data handling outside the corporate network.
Beyond the region, GDPR, HIPAA, and PCI DSS follow the data, not the office location. When employees relocate across jurisdictions during conflict, data residency rules can be violated. Audit trails become incomplete when monitoring tools are not extended to remote endpoints. Access reviews skipped under pressure leave excessive permissions undetected for months.
Organizations that treat compliance as an ongoing operational discipline are far better positioned to demonstrate control continuity when it matters most, during an audit, after an incident, or in a regulatory review.
What Effective Security Looks Like
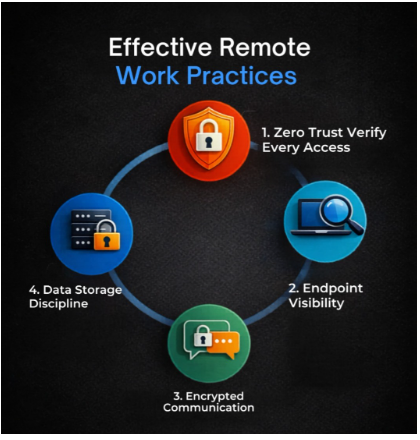
Zero Trust is not optional in remote environments. The assumption that users inside a network are trustworthy was always a weak foundation; in a remote-first or emergency-remote scenario, it collapses entirely. Every access request should be verified based on identity, device health, and context, not network location. Implementing multi-factor authentication across all corporate systems is the minimum baseline.
Endpoint visibility must extend to remote devices. Organizations need to know which devices are connecting to their systems, what software is running on them, and whether they meet security standards. Endpoint detection and response tools, combined with mobile device management policies, give security teams the visibility they need to act quickly when something looks wrong.
Encrypted communication is non-negotiable. Employees operating in conflict zones or using consumer internet connections should only communicate through encrypted channels. This applies to email, file transfers, and video calls. Any sensitive data exchanged outside an encrypted channel should be treated as potentially compromised.
Cloud storage discipline matters. One of the most common compliance failures in remote work scenarios is employees saving work files to personal cloud accounts, Google Drive, iCloud, Dropbox, because it is faster or more convenient. Organizations need a single approved cloud repository with access controls, and employees need to know that deviating from it creates real legal and security exposure.
The Human Factor
The UAE Cybersecurity Council stated plainly that the human element remains the first line of defence. Technical controls are necessary but insufficient on their own. An employee who clicks a phishing link, reuses a password, or stores sensitive files in an unapproved location can undermine sophisticated security architecture in minutes.
Conflict conditions make this worse. People under stress make faster, less careful decisions. They are more likely to respond to urgent-sounding messages without verifying their source. Structured compliance training for distributed teams, covering phishing recognition, credential hygiene, and data handling, directly reduces incident rates. Both the UAE IAR and Saudi Arabia’s ECC include employee cybersecurity awareness as a mandatory control requirement, not an optional recommendation.
Organizations must build clear, low-friction reporting mechanisms so employees can flag suspicious activity without hesitation. The Council’s advisory emphasized that prompt reporting of phishing attempts is essential to protecting both organizational and national digital infrastructure.
Incident Response Must Account for Remote Conditions
An incident response plan built for a co-located team often breaks down when applied to a dispersed workforce dealing with a concurrent crisis. The first hours after a breach are the most critical. Organizations frequently lose that time simply establishing who is responsible for what.
Plans must be tested in conditions that reflect how the organization actually operates under pressure. Tabletop exercises simulating a breach during a remote-work scenario, with team members in different locations, on different devices, with potentially degraded communication channels, expose gaps that are simple to fix in advance and extremely costly to discover during an active incident. The UAE IAR’s incident management controls and Saudi Arabia’s TCC both require documented, tested incident response procedures.
Conclusion
Remote work creates openings that attackers move into fast. A 40 percent rise in remote-work-related incidents is not a trend to monitor. It is a signal to act on.
For organizations in the UAE and Saudi Arabia, the stakes are higher than most. The IAR, NESA’s Information Assurance Standards, and Saudi Arabia’s NCA Telework Cybersecurity Controls are not voluntary frameworks, they carry real penalties, and regulators do not grade on a curve during a crisis. The organizations that get caught flat-footed are typically the ones that treated compliance as something to tidy up after the dust settles.
Remote work security is not a checklist you run through once and file away. Attackers are consistent. Regulators are consistent. Your security posture needs to be too, whether your team is in the office, working from home, or operating through a regional disruption that nobody planned for.




 Governance and Policy Management
Governance and Policy Management