Compliance Implications of State-Linked Cyber Breaches

State-linked cyber operations have shifted from isolated incidents to coordinated campaigns tied to geopolitical events. Recent tensions across the Middle East have shown how quickly cyber activity can escalate alongside physical conflict. Organizations operating in or connected to affected regions face a different class of risk. These are not opportunistic attacks. They are targeted, persistent, and often aligned with strategic objectives.
For compliance teams, this changes the equation. Security incidents tied to state-backed actors carry broader implications than standard breaches. They expose gaps in governance, third-party oversight, and regulatory readiness.
When Cyber Incidents Become Geopolitical Events
State-linked breaches rarely exist in isolation. They often target sectors that support national infrastructure, financial systems, or supply chains. In the current Middle East climate, organizations connected to regional operations, vendors, or infrastructure face increased exposure even if they are not directly involved in the conflict.
Attackers use these connections to expand their reach. A vendor operating in a high-risk region may become the entry point into a larger ecosystem. Once access is gained, the objective shifts from disruption to persistence and intelligence gathering.
This type of breach places organizations under scrutiny beyond technical impact. Regulators expect clear accountability. Stakeholders expect transparency. The incident becomes a governance issue as much as a security event.
The Breach Is Only the Beginning
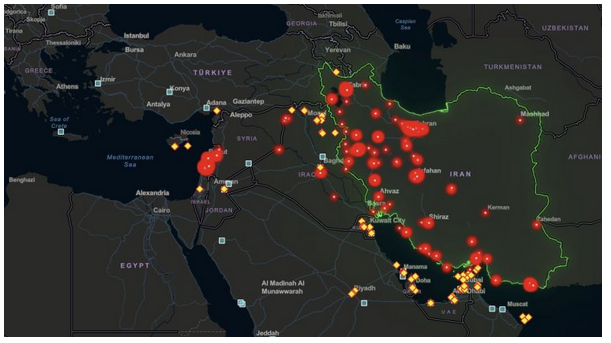
State-linked cyber operations in the Middle East follow a clear pattern; they do not discriminate by corporate neutrality. Over 70 hacktivist groups launched campaigns during the February 2026 escalation, deploying DDoS attacks, website defacements, credential theft, and disinformation operations, with supply chain interconnections pulling countries far outside the region into the blast radius.
What makes this escalation distinct from past conflicts is the parallel cyber campaign running alongside the kinetic activity, described by analysts as one of the largest coordinated digital offensives recorded. An AWS data centre serving government, finance, and enterprise clients was among the infrastructure affected.
When that kind of event hits a vendor your organisation depends on, regulators offer no grace period. The compliance clock starts at the moment of discovery, not attribution, not remediation
The Supply Chain Is the Entry Point
Iranian APT groups have long preferred supply chain access over direct intrusion. It is quieter, harder to attribute, and exploits the trust that organisations extend to their vendors by default. MuddyWater (also tracked as Mango Sandstorm), OilRig, and Charming Kitten have all demonstrated in 2026 what security researchers have been documenting since at least 2024, a sustained, methodical focus on vendors, cloud providers, and third-party contractors as the path into high-value targets.
In the weeks following the February 2026 escalation, pro-Iranian hacktivist group DieNet claimed DDoS attacks against airports in Bahrain and the UAE, and targeted Riyadh Bank and the Bank of Jordan. Hydro Kitten, operating on behalf of the Islamic Revolutionary Guard Corps, signalled plans to target the financial sector specifically. A cyberattack disrupted operations at Stryker, a major U.S. medical technology company, with Iran-aligned hackers identified as the likely source. These are not isolated incidents. They are part of a coordinated, multi-vector campaign in which third-party vendors and cloud infrastructure sit squarely in the crosshairs.
The AWS data centres in the UAE and Bahrain were physically targeted by Iran’s IRGC. Businesses relying on those cloud services suffered disruptions they did not control and could not have prevented at the network level. That dependency, and the compliance exposure it creates, is exactly the kind of concentration risk that current regulatory frameworks are now requiring organisations to map and manage.
Regulatory expectations during state-linked incidents
Regulators do not distinguish between causes of breach when evaluating compliance. Whether an attack originates from a criminal group or a state-backed actor, organisations remain responsible for maintaining controls, protecting data, and reporting incidents within defined timelines.
However, state-linked breaches often trigger additional scrutiny.
Authorities may require:
- Faster incident reporting
- Detailed forensic evidence
- Proof of control effectiveness
- Clear documentation of third-party risk management
In regions such as the UAE and Saudi Arabia, regulatory bodies have already issued advisories emphasizing the need for heightened vigilance during periods of geopolitical tension. These advisories highlight the expectation that organizations adjust controls in response to elevated risk levels.
Failure to do so can lead to regulatory penalties even if the breach itself was sophisticated or difficult to prevent.
The compliance gap exposed by state-linked attacks
State-backed operations reveal weaknesses that routine audits may not surface.
Many organisations maintain documented compliance programs that perform well under standard conditions. Controls are defined, risks are assessed, and evidence is collected periodically. During targeted attacks, these programs are tested under pressure.
Common gaps include:
- Delayed detection due to limited visibility across vendors
- Incomplete asset and access inventories
- Static risk assessments that do not reflect changing geopolitical conditions
- Weak integration between security operations and compliance reporting
These gaps do not originate from a lack of effort. They result from compliance models built for stability rather than disruption.
HOW A STATE-LINKED BREACH CREATES COMPLIANCE EXPOSURE
State-linked group identifies third-party vendor as access point → Vendor systems compromised via spear phishing, credential harvesting, or unpatched vulnerability → Attacker moves laterally into primary organisation — often undetected for weeks or months → Discovery triggers mandatory breach notification requirements → Regulators assess: Was vendor risk properly identified, managed, and reported?
Note: The longer the dwell time, the more difficult it becomes to demonstrate timely awareness, which is itself a compliance requirement across every major regional framework.
From static compliance to continuous control
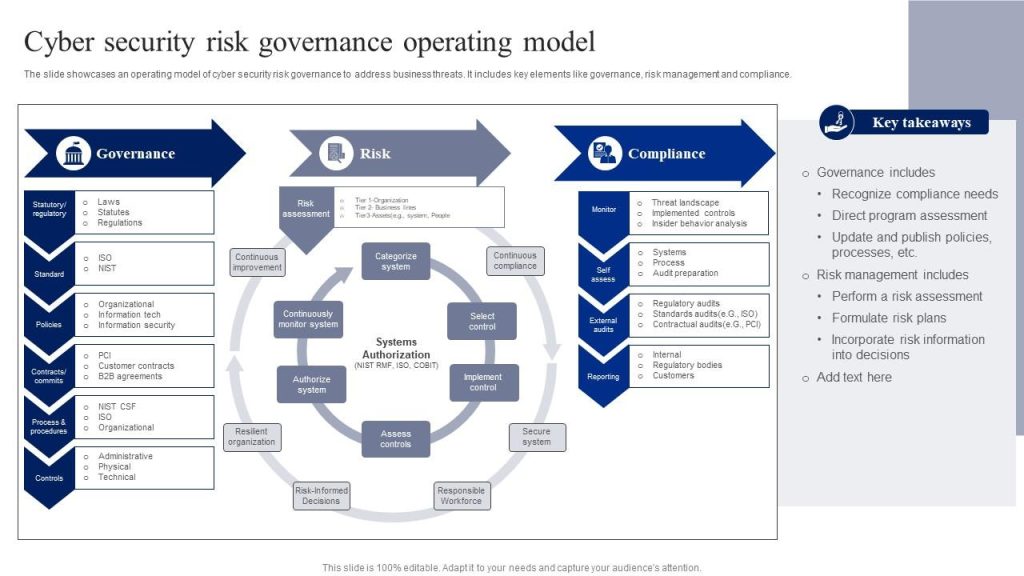
Addressing state-linked risk requires a shift in how compliance is managed. Static frameworks cannot keep pace with dynamic threats tied to geopolitical events.
Organisations need continuous control and monitoring. Risk assessments must be updated as conditions change. Third-party exposure must be tracked in real time.
This is where structured governance platforms provide value. By connecting controls, risks, and evidence into a unified system, organisations gain visibility into how compliance holds under changing conditions.
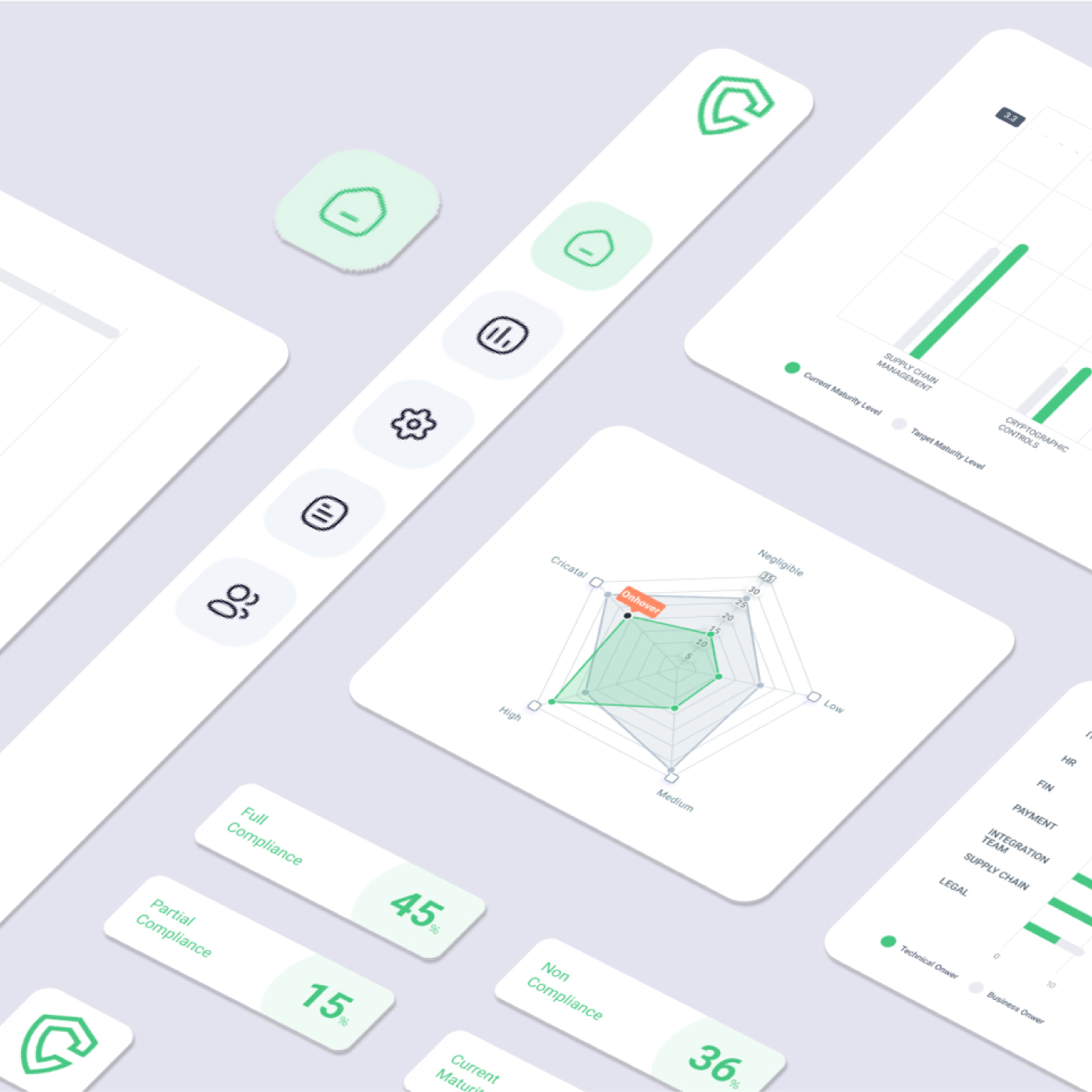
Complyan enables organisations to maintain this visibility by aligning regulatory requirements with operational controls. Instead of treating compliance as a periodic exercise, controls are monitored continuously and mapped across frameworks.
This approach allows organisations to identify gaps early and adjust controls before they become regulatory issues.
Linking cyber risk to business impact
State-linked breaches often target areas that affect business continuity. Supply chain disruption, data exposure, and operational downtime are common outcomes.
Compliance programs must therefore extend beyond regulatory alignment. They must connect cybersecurity risk to business impact.
A structured risk management approach allows organizations to evaluate which assets are most critical, which vendors introduce the highest exposure, and which controls reduce risk effectively.
Through integrated cyber risk management, organizations can prioritize actions based on real exposure rather than theoretical risk models.
This ensures that compliance efforts support operational resilience.
Preparing for the next phase of cyber conflict
The recent surge in cyber activity linked to geopolitical tension is unlikely to remain temporary. As conflicts persist, cyber operations will continue to play a central role.
Organizations must assume that exposure extends beyond their internal systems. Vendors, partners, and regional dependencies all contribute to overall risk posture.
Preparation involves more than strengthening defenses. It requires aligning governance, risk management, and compliance with real-world conditions.
This includes:
- Continuous monitoring of third-party risk
- Faster incident detection and reporting
- Stronger alignment between security operations and compliance teams
- Clear documentation that reflects actual control performance
Conclusion
2026 is a turning point. Regulators across the region are shifting from guidance to enforcement, making compliance a board-level responsibility.
Frameworks from NCA and SAMA now place clear accountability on executives. If a breach occurs through a third party and geopolitical risk wasn’t properly assessed, it becomes a regulatory failure, not just a security issue.
Organisations that will hold up are those treating vendor risk as a live, evolving factor. That means understanding where vendors operate, extending compliance requirements across the supply chain, and building realistic incident response plans.
Threat actors are targeting trusted vendor relationships. The frameworks already demand the right response; the real question is whether organisations are executing.




 Governance and Policy Management
Governance and Policy Management