Why Compliance Is the Cheapest Insurance Policy Your Organisation Has Right Now

Cyber insurance has become a standard line item in many budgets. Premiums are rising. Coverage is tightening. Insurers are asking more questions before they agree to cover anything.
At the same time, many organisations still treat compliance as a reporting task. Something to prepare for audits. Something to document and file away.
That approach is expensive.
Compliance, when done properly, functions as a form of risk transfer before insurance even comes into play. It reduces the likelihood of incidents, limits impact when they occur, and directly affects how insurers assess your organisation.
In practical terms, it is the cheapest insurance policy you already have.
The Premium Problem Nobody Talks About
Cyber insurance underwriters are not in the business of charity. Before they price a policy, they conduct a detailed assessment of your security posture. They look at whether multi-factor authentication is deployed, how you handle access controls, whether you have documented incident response procedures, how you manage third-party vendor risk, and critically, whether you are aligned with any recognised security framework.
The result of that assessment determines your premium. And organisations with weak compliance postures are not just paying more, some are being denied coverage altogether.
IBM’s data on breach costs consistently puts the average damage from a data breach at well over $4 million. Against that figure, the cost of implementing a solid compliance programme looks like a rounding error. The calculation is not complicated: organisations that reduce their risk profile through compliance pay less for insurance and lose less when incidents occur. Those that don’t, pay in both directions.
The Shift in Cyber Insurance Expectations
Cyber insurance providers have changed how they evaluate risk.
A few years ago, coverage could be secured with basic questionnaires. Today, insurers expect evidence. They want to see how controls operate, not just how they are described.
Common requirements now include:
- Multi-factor authentication across critical systems
- Endpoint protection and monitoring
- Incident response readiness
- Regular vulnerability management
- Third-party risk oversight
If these controls are weak or inconsistent, premiums increase. In some cases, coverage is denied.
Insurance is no longer a fallback. It is tied directly to your security posture.
Compliance Reduces the Variables Insurers Price Against
Insurance pricing is fundamentally a risk calculation. The more unpredictable your security behaviour, the higher the premium required to justify covering you. Compliance frameworks — whether ISO/IEC 27001, NIST CSF, SOC 2, GDPR, or industry-specific standards like HIPAA or PCI DSS, exist precisely to make your security behaviour predictable, documented, and defensible.
When an underwriter sees that your organisation has achieved ISO 27001 certification, they are not just impressed by the badge. They are reading a signal that your team has systematically assessed cyber risks, implemented controls, trained staff, and committed to continuous improvement. That signal translates directly into a more favourable policy.
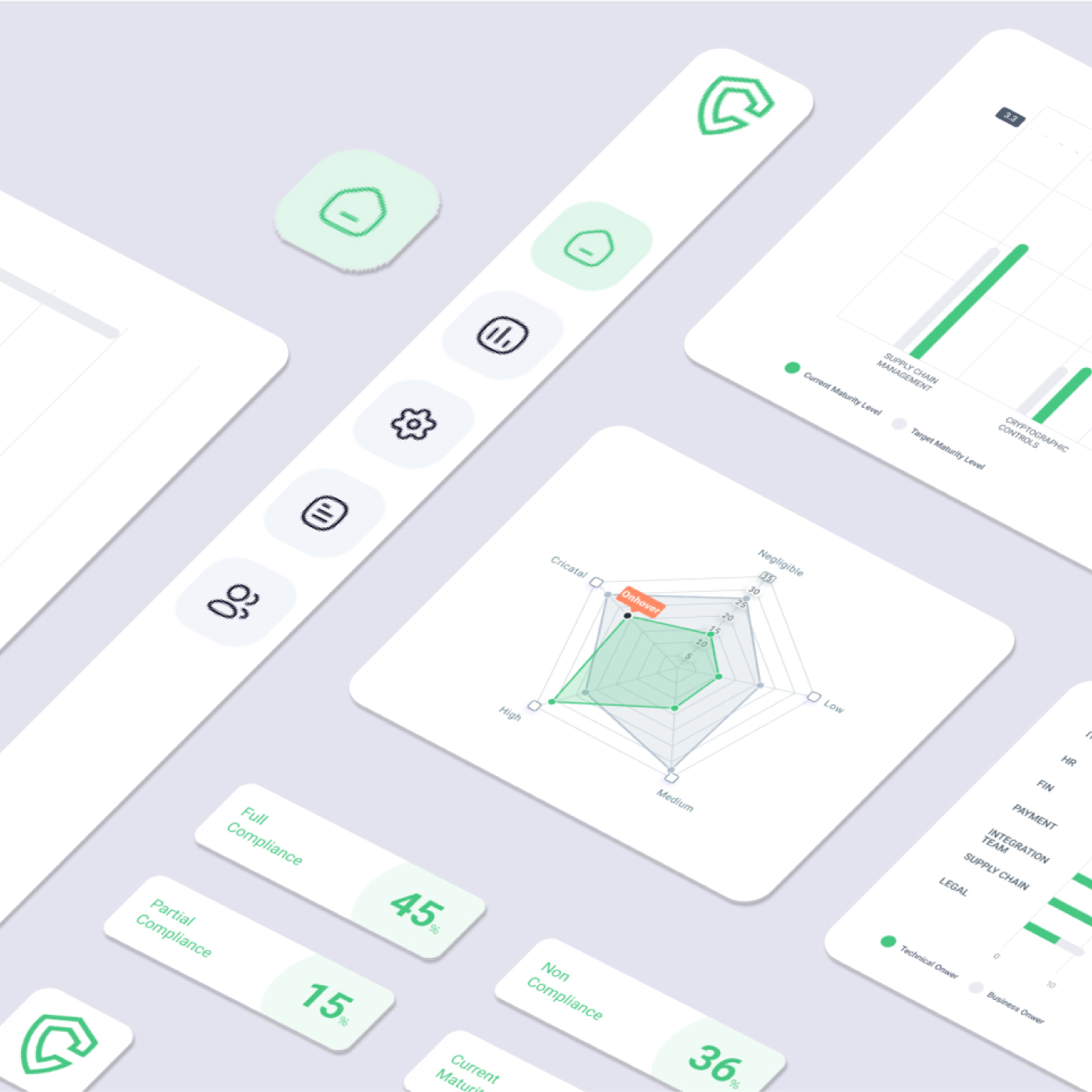
Complyan’s cybersecurity compliance break down how compliance frameworks map to real risk reduction, showing organisations how structured adherence to recognised standards creates measurable security improvements the exact kind insurers reward.
The Controls That Move the Needle Most
State-backed operations reveal weaknesses that routine audits may not surface.
Many organisations maintain documented compliance programs that perform well under standard conditions. Controls are defined, risks are assessed, and evidence is collected periodically. During targeted attacks, these programs are tested under pressure.
Common gaps include:
- Delayed detection due to limited visibility across vendors
- Incomplete asset and access inventories
- Static risk assessments that do not reflect changing geopolitical conditions
- Weak integration between security operations and compliance reporting
These gaps do not originate from a lack of effort. They result from compliance models built for stability rather than disruption.
The Controls That Move the Needle Most

Not all compliance activities have equal weight in the eyes of an insurer. Some controls are now considered baseline requirements rather than differentiators, you will struggle to get covered without them, let alone get a discount.
Multi-factor authentication tops almost every underwriter’s checklist. The reason is simple: the majority of network compromises begin with stolen credentials. MFA interrupts that attack path before it starts. Organisations that have deployed MFA across all privileged accounts and remote access points consistently see better coverage terms.
Documented incident response planning is another area where compliance discipline pays off directly. An insurer reviewing your application wants to see evidence that your team knows exactly what to do when something goes wrong. A tested, documented IR plan shortens breach response times, limits damage, and reduces the ultimate claim size — all of which benefit both parties.
Vendor risk management has moved from best practice to insurance requirement in many sectors. With a third of all data breaches in recent years traced back to compromised third-party vendors, insurers are scrutinising how organisations manage their supply chain security. Organisations that have formalised vendor risk assessment processes — regular reviews, security questionnaires, ongoing monitoring — demonstrate the kind of supply chain hygiene that reduces exposure significantly.
Employee security awareness training rounds out the core controls. Human error remains the entry point for the majority of successful attacks. Organisations that run regular, documented security awareness training, including phishing simulations, signal to insurers that they have addressed this vulnerability systematically rather than hoping for the best.
Preventing Loss Before It Needs Coverage
Insurance responds after an incident, Compliance reduces the chance that the incident occurs at all.
Consider a ransomware scenario. An organisation with weak access controls, inconsistent patching, and no segmentation is an easy target. Recovery is expensive. Downtime impacts operations. Insurance may cover part of the loss, but not all of it.
Now consider the same organisation with enforced access controls, tested backups, and network segmentation. The attack either fails or is contained quickly.
The difference is not the insurance policy. It is the control environment.
Solutions like Cyber Risk Management help organisations identify where those control gaps exist and prioritise remediation based on risk impact, not just audit requirements.
Compliance as a Business Advantage, Not Just a Safety Net
The conversation about compliance too often centres on avoiding negative outcomes, fines, breaches, failed audits. The more accurate frame is financial leverage. Organisations that treat compliance programmes as operational investments are building a track record that reduces insurance costs year over year, creates evidence for better policy terms at renewal, improves their standing during vendor due diligence, and demonstrates governance maturity to clients, boards, and regulators.
This is the strategic case for cyber risk management that many boards are still missing. Risk management is not a technical function sitting in the IT department. It is a business function with direct financial consequences, and compliance is the engine that drives it.
Where to Start If Your Compliance Programme Is Immature
For organisations that have largely reactive security postures, the priority is not to boil the ocean. Start with what insurers actually ask about.
Map your current controls against a recognised framework, NIST CSF is a practical starting point because of its broad industry acceptance. Identify the gaps between your current state and the framework’s requirements. Prioritise the controls that directly correspond to the questions on a typical cyber insurance application: MFA, endpoint protection, patch management, privileged access management, data backup procedures, and incident response planning.
Document everything. An insurer cannot credit you for work they cannot verify. Every security training session, every audit, every penetration test, every policy update, these create the paper trail that converts your compliance investment into negotiating leverage.
Then engage your insurance broker proactively. Many carriers offer loss-control consultation services that help organisations identify specific gaps affecting their premium. Those recommendations, when acted on, often translate into immediate credits at the next renewal.
Conclusion
For organisations that have largely reactive security postures, the priority is not to boil the ocean. Start with what insurers actually ask about.
Map your current controls against a recognised framework, NIST CSF is a practical starting point because of its broad industry acceptance. Identify the gaps between your current state and the framework’s requirements. Prioritise the controls that directly correspond to the questions on a typical cyber insurance application: MFA, endpoint protection, patch management, privileged access management, data backup procedures, and incident response planning.
Document everything. An insurer cannot credit you for work they cannot verify. Every security training session, every audit, every penetration test, every policy update, these create the paper trail that converts your compliance investment into negotiating leverage.
Then engage your insurance broker proactively. Many carriers offer loss-control consultation services that help organisations identify specific gaps affecting their premium. Those recommendations, when acted on, often translate into immediate credits at the next renewal.




 Governance and Policy Management
Governance and Policy Management