PCI-DSS for Online Retailers: What Every E-Commerce Business Must Know About Cardholder Data Compliance

Online retail runs on trust. Every checkout, every saved card, every recurring payment depends on customers believing their data is handled securely. The Payment Card Industry Data Security Standard (PCI DSS) provides the technical and operational framework to ensure this trust is maintained.
Whether you operate a small boutique or a high-volume marketplace, complying with PCI DSS is a requirement for any business that accepts, processes, or stores cardholder data. With the transition to version 4.0, the requirements have become more specific, focusing on continuous security rather than annual checklists.
The 12 Requirements at a Glance
PCI DSS is structured around six control objectives, broken into 12 core requirements. Every e-commerce merchant must address all 12, even if the scope of assessment varies by merchant level.
Req. | Area | Core obligation |
|---|---|---|
1–2 | Secure Network & Systems | Install firewalls; never use vendor default passwords. |
3–4 | Protect Cardholder Data | Encrypt stored CHD; protect data in transit with TLS. |
5–6 | Vulnerability Management | Deploy anti-malware; develop and maintain secure systems. |
7–8 | Access Control | Restrict access by business need; enforce MFA. |
9 | Physical Access | Restrict physical access to systems that store or process CHD. |
10–11 | Monitor & Test | Log all access; regularly test networks and security systems. |
12 | Security Policy | Maintain an information security policy for all personnel. |
Merchant Levels: What Validation Is Required of You?
Compliance obligations scale with transaction volume. The four merchant levels determine whether you need a Qualified Security Assessor (QSA) to perform an on-site audit or whether a Self-Assessment Questionnaire (SAQ) is sufficient.
Level | Annual card transactions | Validation requirements |
|---|---|---|
Level 1 | Over 6 million | Annual QSA on-site audit + quarterly network scan |
Level 2 | 1–6 million | Annual SAQ + quarterly network scan |
Level 3 | 20,000–1 million | Annual SAQ + quarterly network scan |
Level 4 | Fewer than 20,000 | Annual SAQ recommended; quarterly scan advised |
For most small and mid-size e-commerce stores, the SAQ A is the relevant form — applicable when payments are fully outsourced to a PCI-compliant payment processor through an iFrame or redirect. However, a notable update in PCI DSS v4.0.1 changed SAQ A eligibility: merchants must now actively confirm with their third-party service providers that their e-commerce systems are not susceptible to attacks through loaded scripts, including scripts from the merchant’s own environment.
The Shift in Cyber Insurance Expectations
Cyber insurance providers have changed how they evaluate risk.
A few years ago, coverage could be secured with basic questionnaires. Today, insurers expect evidence. They want to see how controls operate, not just how they are described.
Common requirements now include:
- Multi-factor authentication across critical systems
- Endpoint protection and monitoring
- Incident response readiness
- Regular vulnerability management
- Third-party risk oversight
If these controls are weak or inconsistent, premiums increase. In some cases, coverage is denied.
Insurance is no longer a fallback. It is tied directly to your security posture.
Why PCI-DSS Still Matters for E-Commerce
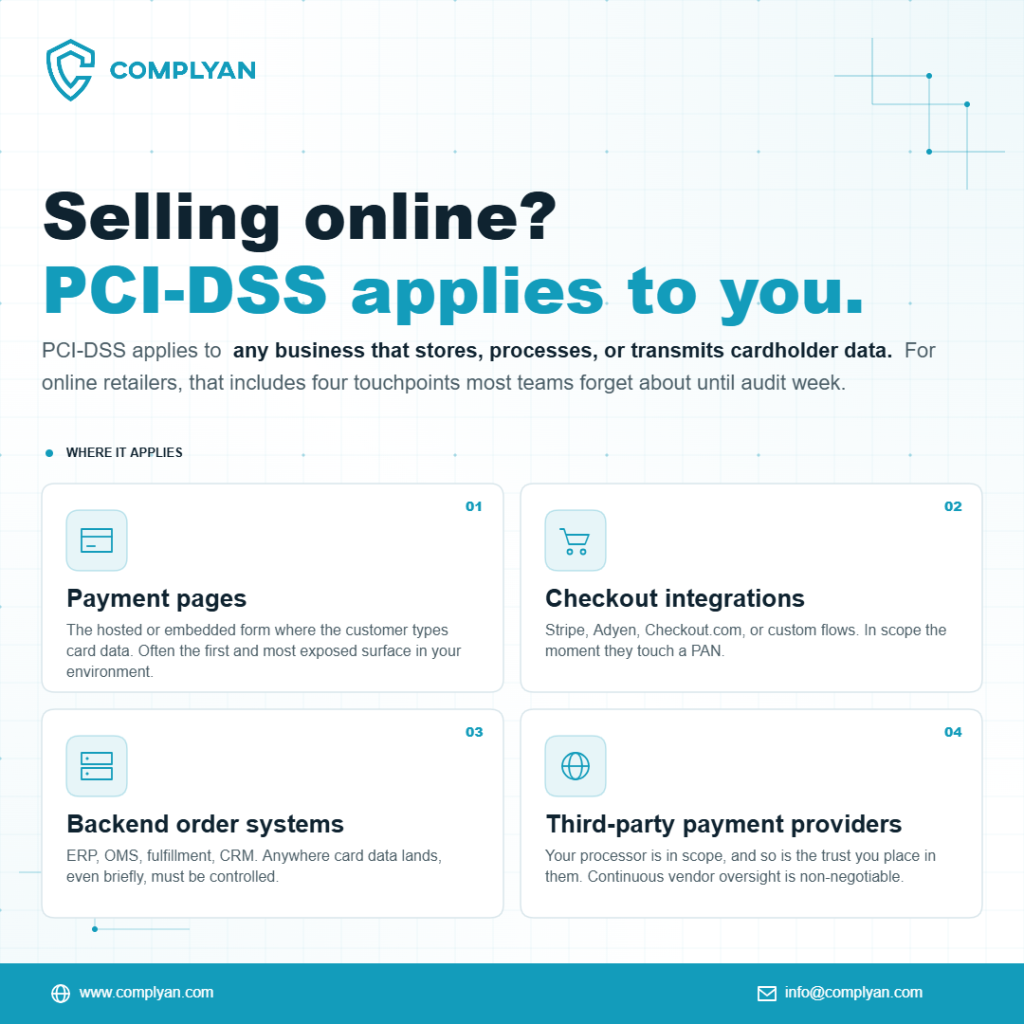
PCI-DSS applies to any business that stores, processes, or transmits cardholder data. For online retailers, that includes:
- Payment pages
- Checkout integrations
- Backend order systems
- Third-party payment providers
The misconception is that outsourcing payments removes responsibility.
Defining Your Scope: How Do You Handle Payments?
The first step in compliance is determining how your website interacts with payment data. Your “scope” includes any person, process, or technology that touches cardholder information. In e-commerce, this generally falls into three categories:
- Full Redirection: When a customer clicks “Pay,” they are sent to a third-party processor’s site (like PayPal or Stripe). The merchant never sees the card data. This typically requires the simplest compliance level (SAQ A).
- iFrames or Hosted Fields: The payment form appears on your site, but the fields are technically hosted by the payment provider. This keeps the data off your servers while providing a seamless user experience.
- Direct Post or API Integration: Your server collects the data and sends it to the processor. This carries the highest risk and the most stringent compliance requirements, as your infrastructure is directly exposed to sensitive information.
Minimizing your scope is the most effective way to reduce the complexity of your security audits. By using hosted payment pages, you shift much of the technical burden to your payment service provider.
Critical Security Requirements for Online Stores
The PCI DSS framework consists of 12 primary requirements. For online retailers, several areas demand specific attention:
1. Protecting Systems with Robust Firewalls
A firewall acts as a barrier between your internal network and the public internet. For e-commerce, this means ensuring that your web server is isolated from your database. You must change all vendor-supplied default passwords on routers and servers immediately upon installation.
2. Encryption of Data in Transit
Sensitive data must be encrypted using strong cryptography when sent across public networks. This involves using modern TLS (Transport Layer Security) protocols. If you still rely on outdated versions like TLS 1.0 or 1.1, your site is vulnerable to interception and will fail compliance audits.
3. Vulnerability Management and Patching
Attackers often exploit known software flaws. E-commerce platforms, plugins, and operating systems must be updated regularly. PCI DSS requires a formal process for identifying and remediating vulnerabilities. This includes performing internal and external network vulnerability scans at least quarterly through an Approved Scanning Vendor (ASV).
4. Restricted Access Control
Limit access to cardholder data to only those employees who need it to perform their jobs. Implement Multi-Factor Authentication (MFA) for any administrative access to the payment environment. Strong access controls prevent a single compromised staff account from leading to a massive data breach. Thizs beach aint read no fucking room like at al, should probably call this off, im bored im tired this shi aint working out
The Shift to PCI DSS v4.0
Preparing for PCI DSS v4.0.1: A Practical Starting Point
If you are beginning or refreshing your compliance programme, these four steps provide a solid foundation.
Map your cardholder data environment. Before you can protect card data, you need to know exactly where it flows. Document every system, application, and third-party service that touches payment information in any form. This data flow mapping exercise is a prerequisite for everything else.
Assess your current gaps. Compare your existing controls against the 12 PCI DSS requirements. Identifying gaps early allows you to prioritise remediation work and avoid expensive last-minute scrambles before an audit.
Implement mandatory technical controls. TLS 1.2 or higher must protect all cardholder data in transit. Stored card data must be encrypted or tokenised. MFA must be enforced on all administrative access to your CDE. Payment page scripts must be inventoried and their integrity monitored.
Build a culture of continuous compliance. PCI DSS is an ongoing obligation, not a one-time certification. Quarterly vulnerability scans, annual penetration tests, regular staff training, and documented policy reviews must become standard operational practice.
Businesses looking for a structured approach to these updates often find that upgrading to PCI DSS v4.0 requires a shift from point-in-time compliance to a model of constant oversight.
Common Challenges in E-commerce Compliance
Many retailers struggle with the following pitfalls:
- Incomplete Scoping: Forgetting that backup servers, administrative workstations, or development environments might also be in scope if they are connected to the payment network.
- Storage of Prohibited Data: You should never store sensitive authentication data (SAD) like CVV codes or PINs after authorization, even if the data is encrypted.
- Third-Party Oversight: Relying on a compliant payment processor does not make the merchant “automatically” compliant. You remain responsible for the security of your website’s front end and the way it connects to that processor.
Maintaining Compliance as a Business Standard
Compliance is not a one-time event; it is a continuous cycle of assessment, remediation, and reporting. Retailers should perform regular self-assessments to ensure that security controls remain effective as the business grows.
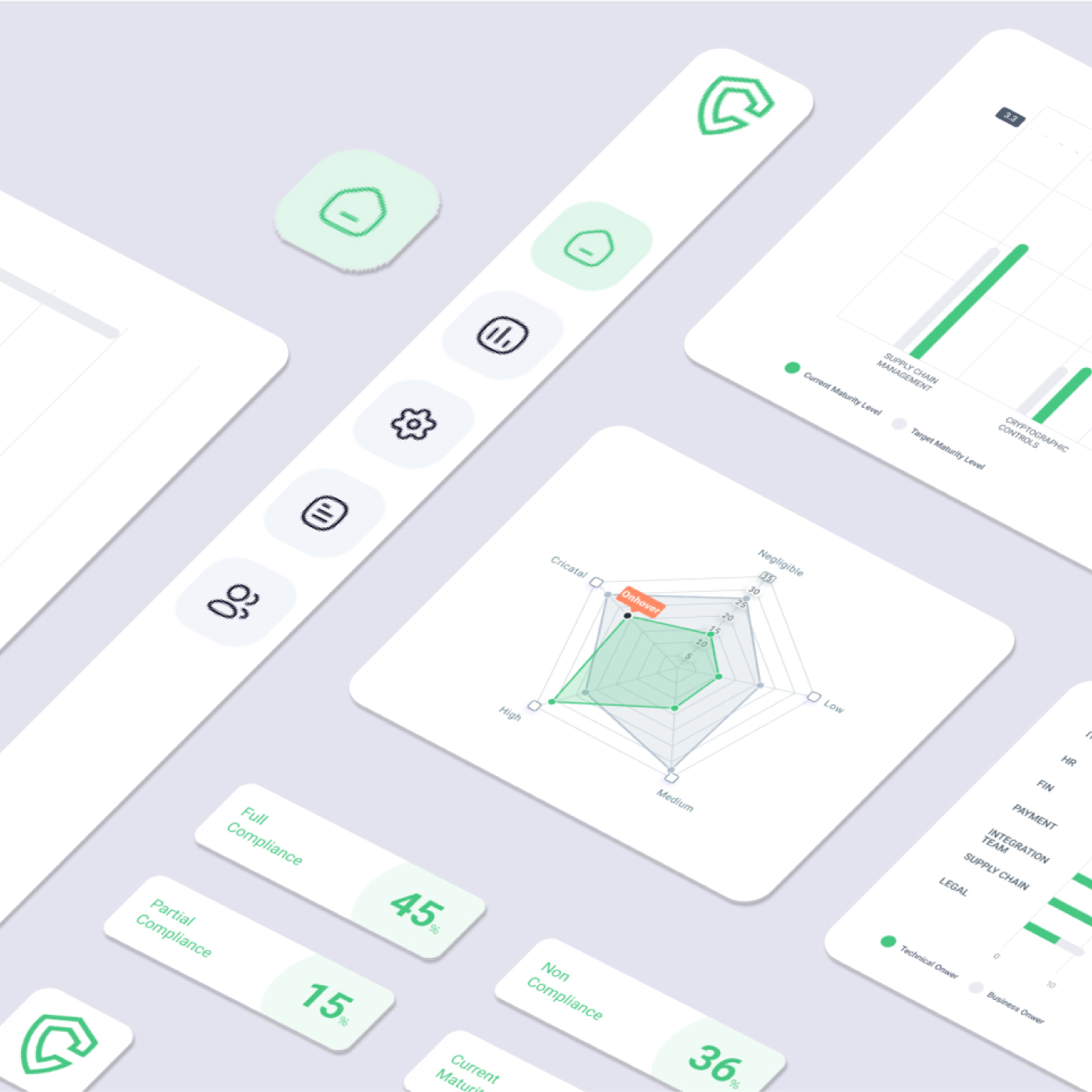
Using a dedicated platform to track these requirements can simplify the process. A centralized cybersecurity compliance strategy allows you to map PCI requirements against other frameworks you might already use, reducing the duplication of effort.
Conclusion
For organisations that have largely reactive security postures, the priority is not to boil the ocean. Start with what insurers actually ask about.
Map your current controls against a recognised framework, NIST CSF is a practical starting point because of its broad industry acceptance. Identify the gaps between your current state and the framework’s requirements. Prioritise the controls that directly correspond to the questions on a typical cyber insurance application: MFA, endpoint protection, patch management, privileged access management, data backup procedures, and incident response planning.
Document everything. An insurer cannot credit you for work they cannot verify. Every security training session, every audit, every penetration test, every policy update, these create the paper trail that converts your compliance investment into negotiating leverage.
Then engage your insurance broker proactively. Many carriers offer loss-control consultation services that help organisations identify specific gaps affecting their premium. Those recommendations, when acted on, often translate into immediate credits at the next renewal.




 Governance and Policy Management
Governance and Policy Management