Post-Quantum Cryptography Compliance: What CISOs Need in Their 2026 Roadmap

NIST published the world’s first post-quantum encryption standards, FIPS 203, 204, and 205 in August 2024. Eighteen months later, most enterprise compliance programs still treat quantum-safe cryptography as a 2030 problem. That is a mistake.
The U.S. National Security Agency now expects vendors of network equipment to support and prefer CNSA 2.0 algorithms by 2026. The European Commission’s PQC roadmap requires Member States to begin national strategies by December 31, 2026. PCI DSS 4.0 already mandates that organizations maintain a cryptographic algorithm inventory and a migration plan for deprecated primitives.
Boards are starting to ask the question. Auditors are not far behind.
“The quantum computer doesn’t need to exist yet, the encrypted traffic crossing the wire today does. Traffic encrypted with RSA or classical ECDH in 2024 is compromised against a 2032 quantum adversary, regardless of when the migration starts.”
Why 2026 Is the Pivot Year for PQC Compliance
Three regulatory clocks are now ticking simultaneously, and they sit between September 2026 and January 2027:
- September 21, 2026: FIPS 140-2 moves to historical status, removing it from the federal procurement baseline and forcing module re-validation against FIPS 140-3
- November 2026: CMMC Level 2 enforcement reaches the broader Defense Industrial Base, with cryptographic protection of CUI explicitly in scope
- December 31, 2026: EU Member States must publish national PQC migration strategies under the Commission’s coordinated roadmap
- January 2, 2030: U.S. federal agencies must support PQC algorithms under National Security Memorandum 10, with planning starting now
For any organization selling into government, financial services, healthcare, or critical infrastructure, 2026 is when “we are evaluating PQC” stops being an acceptable answer to a procurement questionnaire or a third-party risk assessment.
The Real Threat: Harvest Now, Decrypt Later
The reason regulators are moving faster than the cryptographically relevant quantum computer is the harvest now, decrypt later (HNDL) attack model. Nation-state actors and sophisticated criminal organizations are intercepting and storing encrypted traffic today, betting that quantum capability later this decade will let them decrypt the archive retroactively.
Federal Reserve research published in 2025 confirms HNDL is no longer theoretical. Any data with a confidentiality lifetime that extends past roughly 2032, patient records, M&A communications, intellectual property, customer PII, government documents — is already exposed if it has crossed the public internet under classical encryption.
That changes the compliance calculus. The question is no longer “when must I migrate?” but “how much of my historical traffic is already lost?”
Where PQC Lands in Your Compliance Frameworks
PQC is not a new control family. It is a re-implementation of cryptographic primitives that already sit inside your existing controls. The work is mapping each framework’s crypto requirement to the new standards:
- NIST CSF 2.0 → PR.DS-01 / PR.DS-02: Add ML-KEM (FIPS 203) for key establishment and ML-DSA (FIPS 204) for digital signatures to your approved cryptography list
- ISO/IEC 27001:2022 → A.8.24 (Use of Cryptography): Update your cryptographic policy to reference NIST PQC standards alongside legacy AES and RSA — see the Complyan guide to ISO 27001:2022 implementation for the underlying control structure
- PCI DSS 4.0 → Requirement 12.3.3: A documented cryptographic inventory and migration plan for deprecated algorithms is already mandatory
- HIPAA Security Rule → §164.312(a)(2)(iv): Address the encryption specification with quantum-safe algorithms for ePHI subject to long retention requirements
- DORA (EU) → Article 9: ICT risk management must account for quantum threats to financial-sector cryptography; the Complyan DORA implementation guide maps Article 9 obligations to operational controls
The audit evidence pattern is consistent across frameworks: a cryptographic bill of materials (CBOM), a documented migration plan with timelines, and evidence of pilot deployments. Modern GRC platforms can map this evidence to controls automatically.
Building the CISO Roadmap: Six Steps for 2026
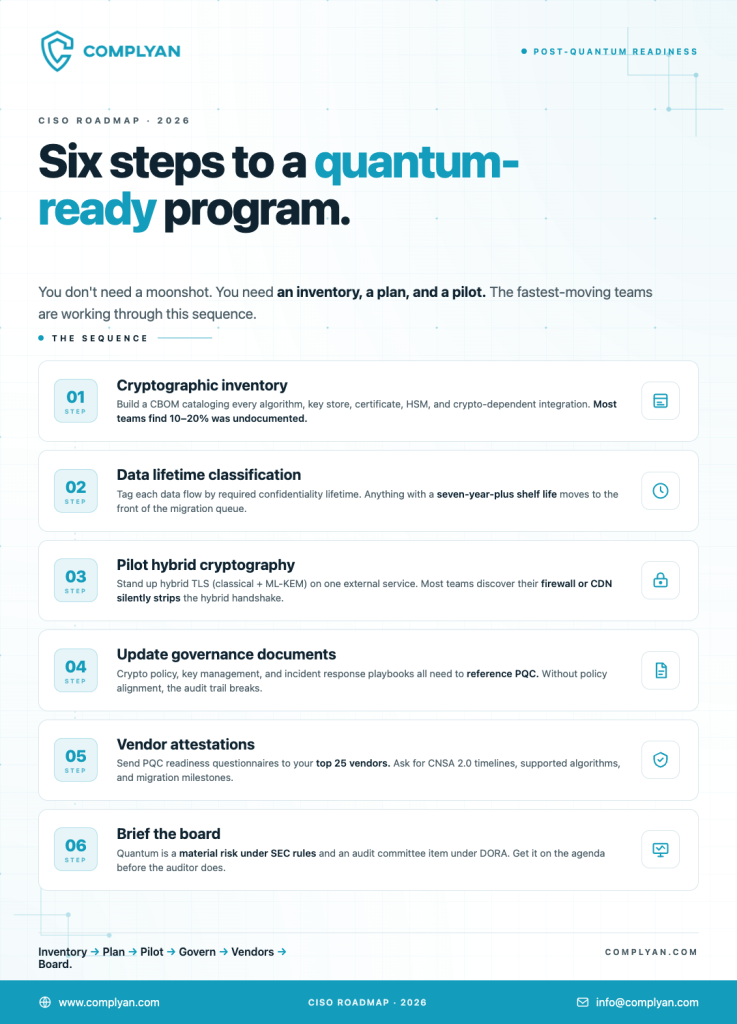
Design for Crypto-Agility, Not Just Migration
ML-KEM and ML-DSA are the current answer, not the final one. NIST selected HQC as a fifth algorithm in March 2025, a code-based KEM designed as a non-lattice backup to ML-KEM, with a final standard expected in 2027. NIST is currently evaluating fourteen additional signature candidates in Round 2 of its on-ramp process with Round 3 finalists expected to be selected later in 2026. The point is not the names. The point is that the standards body itself is still building optionality into the answer.
The architectural lesson from the SHA-1 to SHA-256 migration, and from every TLS version cutover since, is that the next cryptographic migration is always coming. The organizations that absorbed those transitions cheaply were the ones that treated the algorithm as a configuration choice, not a hardcoded assumption.
Crypto-agility means three things in practice:
- Algorithms are abstracted behind interfaces and negotiated at runtime, so swapping ML-KEM-768 for a successor is a config change, not a code change. Hybrid TLS is the working example: the server advertises X25519MLKEM768, the client picks what it supports.
- Certificate and key management systems can issue, rotate, and revoke across multiple algorithm families concurrently. A CA that can sign with both ECDSA and ML-DSA against the same identity is the test.
- The cryptographic inventory is maintained continuously, not refreshed before audits. A point-in-time CBOM is stale the moment the next deployment ships; the inventory has to track changes as they happen, not as they are reported
The Cost of Delay
PQC migration is one of the rare compliance programs where moving fast is actually cheaper than moving late. Hybrid cryptography deployments today cost a fraction of what emergency migrations will cost when a cryptographically relevant quantum computer arrives — and every month of delay extends the HNDL exposure window for data already in transit.
Vendors that wait will face compressed timelines, simultaneous module re-validations, and procurement gates they were not budgeted for. CISOs who start their crypto inventory in 2026 will spend 2028 calmly answering audit questions. The ones still cataloging certificates when the auditor arrives will not enjoy the conversation.
Complyan helps GRC teams operationalize cryptographic inventories, map controls to PQC frameworks, and track migration evidence across ISO 27001, SOC 2, NIST CSF, PCI DSS, and DORA. The NIST CSF 2.0 changes Complyan tracks, including the new Govern function, give GRC teams a control structure to bolt PQC migration evidence onto without reinventing the wheel.




 Governance and Policy Management
Governance and Policy Management