Supply Chain Compliance in Manufacturing: Managing Cyber Risk Across Hundreds of Tier-1 and Tier-2 Vendors

Manufacturing organizations no longer operate within a single controlled environment.
Production systems, logistics providers, raw material suppliers, maintenance contractors, software vendors, and connected industrial technologies now form part of the same operational ecosystem. A modern manufacturer may rely on hundreds of external vendors across multiple regions, all interacting with sensitive systems and operational processes in some way.
That level of dependency has changed how cyber risk spreads across manufacturing environments.
The issue is no longer limited to securing internal infrastructure. Manufacturers now have to manage risk across an extended supply chain where visibility becomes weaker with every additional vendor relationship.
This is why supply chain compliance has become one of the most important cybersecurity priorities in manufacturing.
Why Manufacturing Gets Targeted
According to IBM’s 2026 X-Force Threat Intelligence Index, manufacturing accounted for 27.7% of all cyberattacks observed globally, the highest share of any industry, and the fifth consecutive year the sector has held that position. This is not a reason for alarm; it is a reason to act with the same structured, data-driven approach manufacturers already apply to quality and safety.
The numbers tell a useful story. Exploitation of public-facing applications accounted for 32% of manufacturing breaches, while malware, primarily ransomware, made up 45% of observed attacks. What these figures confirm is that most incidents exploit known, addressable gaps. IBM research found that 85% of manufacturing incidents could have been mitigated with patching, multi-factor authentication, or least-privilege access controls. The opportunity for manufacturers is significant: the same rigour applied to production processes, when applied to vendor security, closes the majority of exposure.
The 2020 SolarWinds incident illustrated why the supplier base matters as much as internal controls. Adversaries compromised a software vendor and from there gained access to thousands of downstream organisations. For manufacturers with complex, multi-tier supplier networks, this kind of indirect exposure makes third-party cyber risk management as strategically important as any other aspect of supply chain governance.
The Tier Problem: Visibility Drops Off Fast
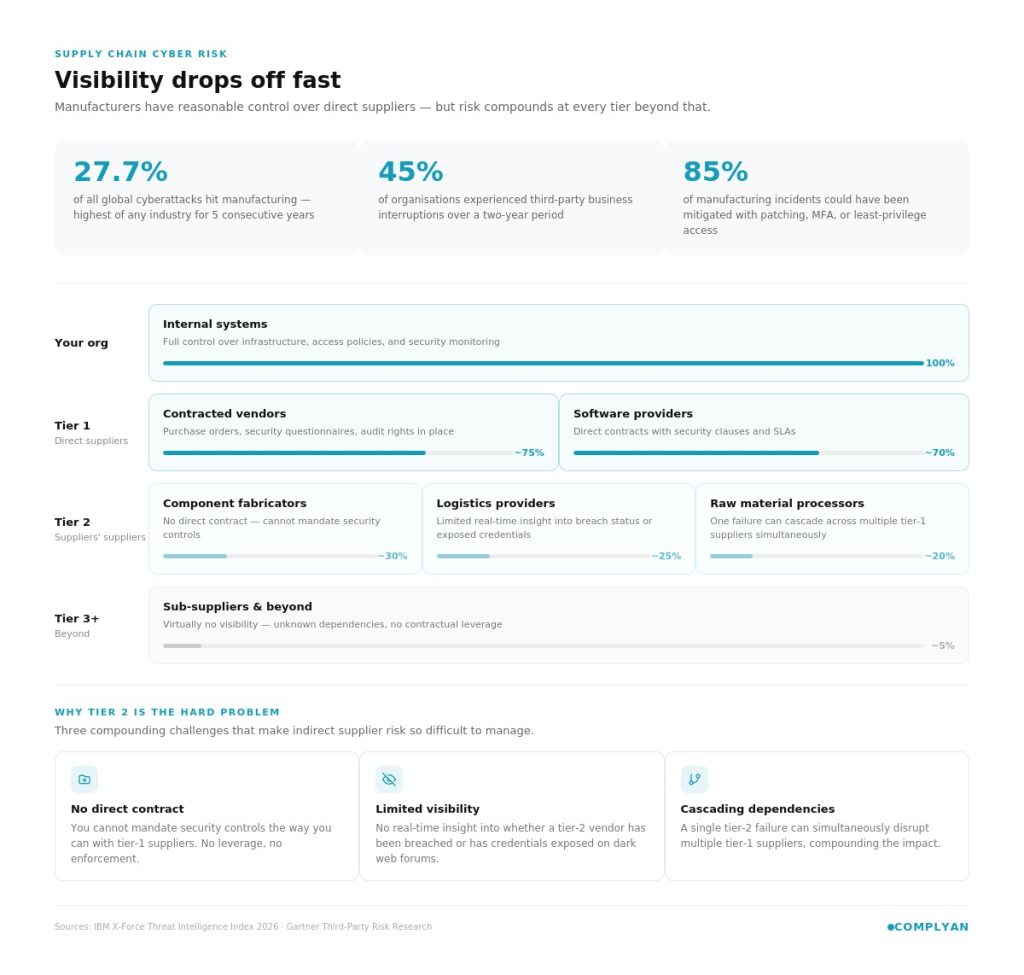
Most manufacturers have reasonable visibility into their tier-1 vendors, the direct suppliers with whom they have contracts, purchase orders, and established relationships. The problem is tier-2 and beyond. These are the suppliers of your suppliers: raw material processors, component fabricators, logistics providers, and software vendors sitting two or three steps removed from your procurement team.
Gartner research found that 45% of organisations across industries experienced third-party-related business interruptions over a recent two-year period. In manufacturing, that figure carries extra weight because third-party failures ripple downstream into production schedules, customer commitments, and regulatory filings.
The challenge with tier-2 vendors is threefold:
- No direct contract relationship means manufacturers cannot mandate security controls the way they can with tier-1 suppliers.
- Limited visibility means most manufacturers have no real-time insight into whether a tier-2 vendor has been breached or has exposed credentials circulating on dark web forums.
- Cascading dependencies mean a single tier-2 failure can simultaneously disrupt multiple tier-1 suppliers.
What Compliance Frameworks Are Required
Regulatory expectations are tightening, and manufacturers who export to Europe or supply to defence and government clients are already feeling it. The EU’s NIS2 Directive explicitly requires organisations in critical sectors, manufacturing included, to assess and manage security risks within their supply chains, not just their own perimeters. DORA, while targeting financial services, signals the direction of travel for all critical infrastructure sectors.
In the United States, NIST SP 800-161 provides a comprehensive framework for Cyber Supply Chain Risk Management (C-SCRM). CMMC (Cybersecurity Maturity Model Certification) is now a hard requirement for defence manufacturers and their sub-contractors, pushing compliance obligations directly into the supplier base.
For manufacturers building a compliance programme from scratch, Complyan’s vendor risk management resources offer structured guidance on mapping regulatory requirements to supplier assessment workflows, a useful starting point before designing your own framework.
Building a Vendor Cyber Risk Programme That Scales
Managing cyber risk across hundreds of vendors requires a programme that is systematic rather than relying on individual heroics. Here is how mature manufacturers are approaching it.
Risk-tiered vendor classification. Not every supplier warrants the same scrutiny. Vendors with direct system access, those processing sensitive IP, or those supplying critical single-source components should sit in a high-risk tier with corresponding controls: security questionnaires, on-site assessments, contractual security requirements, and continuous monitoring. Lower-risk vendors receive lighter-touch assessments calibrated to the actual exposure they represent.
Security questionnaires with teeth. The standard approach of sending a 200-question spreadsheet and filing the responses somewhere is not a programme, it is theatre. Effective questionnaires are scoped to the vendor’s access level, reviewed by someone who can interpret the answers, and followed up with remediation timelines when gaps are found. Platforms that automate questionnaire distribution and scoring dramatically reduce the manual burden at scale.
Continuous monitoring over point-in-time assessments. Annual assessments tell you what a vendor’s security looked like twelve months ago. Security ratings platforms provide ongoing, externally observable signals: open vulnerabilities, misconfigured systems, compromised credentials, and botnet activity associated with vendor infrastructure. This is the only way to maintain real-time awareness across a large vendor population without an unsustainable headcount.
Contractual security requirements. Compliance obligations need to flow into supplier contracts. This includes minimum security standards, the right to audit, breach notification timelines, and incident response obligations. Without contractual hooks, a manufacturer has no leverage when a vendor refuses to remediate a critical finding.
Incident response coordination. When a supplier is breached, most manufacturers find out too late and have no established protocol for responding. A supplier incident response playbook, agreed in advance with key vendors, determines how quickly the impact can be contained.
For organisations looking to operationalise these controls within a governance framework, Complyan’s compliance management platform supports the documentation and workflow management that third-party risk programmes require at scale.
The IT/OT Convergence Complication
Supply chain risk in manufacturing does not stay neatly inside IT systems. As factories integrate Industrial IoT sensors, smart manufacturing systems, and connected robotics, the attack surface extends into operational technology. A compromised vendor providing remote maintenance access to a CNC machine is not just a data breach; it is a production safety issue.
This IT/OT convergence demands that supply chain security programmes account for vendor access to operational networks, not just enterprise IT. Network segmentation, strict access controls for remote vendor connections, and OT-specific security requirements for technology suppliers are essential components of a complete programme.
Conclusion
No manufacturer can achieve perfect visibility across every supplier relationship simultaneously. The pragmatic approach is to start with the vendors whose compromise would hurt most: those with privileged system access, those supplying safety-critical components, and those embedded in production systems. Build the programme there, demonstrate value, then expand coverage outward.
Supply chain compliance in manufacturing is fundamentally a business continuity issue dressed in a security framework. The manufacturers who treat it as such, resourcing it accordingly and embedding it into procurement and vendor management processes, are the ones who keep their production lines running when the next major supply chain incident lands.




 Governance and Policy Management
Governance and Policy Management