The Complete Guide to Cybersecurity Compliance: Cybersecurity Compliance 101.

Regulations don’t wait for organizations to catch up. Fines get issued, audits happen, breaches get reported, and companies without a compliance program in place often find themselves exposed on multiple fronts at once. Cybersecurity compliance gives organizations a structured way to manage these pressures, but its value goes well beyond checking boxes on an audit list.
The purpose of cybersecurity compliance is to guide teams through decisions that might otherwise feel overwhelming. With the right framework, you can prioritize high-impact risks, understand legal responsibilities, and prove to customers and partners that your company handles information responsibly. More than a technical exercise, it is a commitment to safeguard trust and maintain business continuity.
What Cybersecurity Compliance Actually Means
Cybersecurity compliance is the process of aligning an organization’s security controls, policies, and practices with the requirements set out by relevant laws, industry standards, or contractual obligations. These requirements may come from government regulators, industry bodies, or customers who expect a certain level of protection before doing business with you.
At its core, compliance answers a straightforward question: are you doing what you’re supposed to do to protect the data and systems in your care? The answer requires documented evidence, not just good intentions.
It’s worth separating compliance from general cybersecurity. Strong security practices can exist without formal compliance, and compliance can technically be achieved without strong security. The goal is to have both: controls that actually reduce risk, backed by the documentation and governance that regulators and auditors expect.
The Frameworks Organizations Follow
Several frameworks dominate the compliance space, and most organizations are accountable to more than one.
PCI DSS applies to any business that processes, stores, or transmits payment card data. It covers network security, data encryption, access controls, vulnerability management, and regular security testing. Non-compliance can result in the loss of the ability to accept card payments, a significant operational risk for most businesses.
GDPR sets data protection standards for any organization that processes personal data belonging to EU residents. It requires lawful processing, data minimization, breach notification within 72 hours, and the ability to honor individual data rights. The regulation applies globally, a company in Singapore or the UAE processing EU customer data is still subject to GDPR.
ISO 27001 is an internationally recognized information security management standard. Unlike regulatory frameworks, it’s voluntary, but it signals to partners and clients that your security program has been independently verified. Many enterprise contracts now include ISO 27001 certification as a prerequisite.
NIST CSF provides a flexible framework widely used across US federal agencies and private organizations. It organizes security activities around five functions — Identify, Protect, Detect, Respond, and Recover, giving teams a practical structure for managing cyber risk.
NIS2, the EU’s updated network and information systems directive, broadens the scope of who must comply. It now covers sectors including energy, transport, healthcare, food production, and digital infrastructure. Leadership accountability is a key feature: executives are personally responsible for governance failures under NIS2.
Regional Frameworks: The Middle East
For organizations operating in Saudi Arabia and the UAE, regional frameworks carry the same regulatory weight as global ones, and in some sectors, more.
SAMA Cybersecurity Framework (CSF), issued by the Saudi Central Bank, applies to all financial institutions under its supervision, including banks, fintech companies, insurance providers, and credit bureaus. The framework requires documented risk assessments, security governance structures, and periodic self-assessments and audits. It draws on international standards, including NIST, ISO, and PCI DSS, localized to the Saudi financial sector’s specific risk profile.
NCA Essential Cybersecurity Controls (ECC) issued by Saudi Arabia’s National Cybersecurity Authority establishes mandatory minimum cybersecurity requirements for government entities and Critical National Infrastructure operators. The ECC defines 114 controls across five domains: cybersecurity governance, asset management, risk management, people security, and technology protection (NCA, nca.gov.sa). The 2024 update (ECC-2) expanded scope to include financial institutions and private entities hosting CNI, and added controls specifically addressing ransomware, phishing, and alignment with NIST CSF and ISO 27001. Compliance is mandatory and is subject to audit.
Saudi PDPL (Personal Data Protection Law) governed by SDAIA (Saudi Data and AI Authority), covers the collection, processing, and storage of personal data within the Kingdom. It grants individuals rights to access, correct, and request deletion of their data, and mandates breach notifications within required timeframes. Enforcement has been escalating through 2025, and organizations not yet compliant are exposed to public sanctions and forced operational changes.
DESC (Dubai Electronic Security Center) is the regulatory authority for cybersecurity across Dubai’s government and regulated private sector. Its Information Security Regulation (ISR), now at Version 3.0, covers 13 security domains spanning governance, operations, and assurance. Compliance is mandatory for all Dubai government entities, semi-government organizations, and service providers, including cloud, data center, and SOC operators serving government entities. Non-compliance can result in fines up to AED 2 million, operational restrictions, and license suspension (DESC, desc.gov.ae). DESC certification also directly affects government procurement eligibility, making it a business-critical requirement for any company targeting the Dubai public sector.
Organizations operating across both Saudi Arabia and the UAE frequently find themselves accountable to SAMA, NCA ECC, Saudi PDPL, and DESC simultaneously, which is where compliance mapping becomes essential.
Why Compliance Can't Be Treated as a One-Time Project
One of the most common mistakes organizations make is treating compliance as a project with a defined end date. Pass the audit. Get the certificate. Move on. The problem with that approach is that requirements change, systems change, and the risks compliance programs are designed to address don’t stand still.
Continuous compliance monitoring, tracking controls, reviewing policies, and testing systems on an ongoing basis, is what separates organizations that stay compliant from those that scramble every time an audit approaches. Complyan’s cybersecurity compliance platform is built around this idea, giving security teams a centralized way to manage obligations across multiple frameworks without duplicating effort.
Regulators are also paying closer attention. In 2026, enforcement trends across jurisdictions show a clear shift toward holding senior leadership accountable for compliance failures, not just the IT or security function. Board members and C-suite executives are increasingly named in enforcement actions, which changes the conversation from a technical discussion to a business governance issue.
“There’s a distinction I make constantly with clients: passing an audit and actually being secure are two fundamentally different outcomes. An audit tells you where you stand on the day someone checks a list; it doesn’t tell you whether your controls are functioning tomorrow, whether your team knows what to do when something goes wrong, or whether the vendor you onboarded six months ago has quietly become your biggest exposure. The organizations that get this right stop treating compliance as a destination and start treating it as infrastructure. The framework, whether that’s ISO 27001, NIST, or SAMA, etc., gives you the skeleton. The muscle is continuous monitoring, genuine risk ownership at the leadership level, and a team that understands not just what the controls are, but why they exist. Compliance without that security mindset is just paperwork. Frameworks are a starting point, not a finish line.”
— Rabia, Information Security Compliance Consultant
How Complyan Simplifies this Process
Managing compliance across multiple frameworks, SAMA, NCA ECC, DESC, GDPR, ISO 27001, and others, is operationally demanding without the right infrastructure in place. Manual tracking through spreadsheets and siloed documentation increases the risk of gaps, missed deadlines, and failed audits.
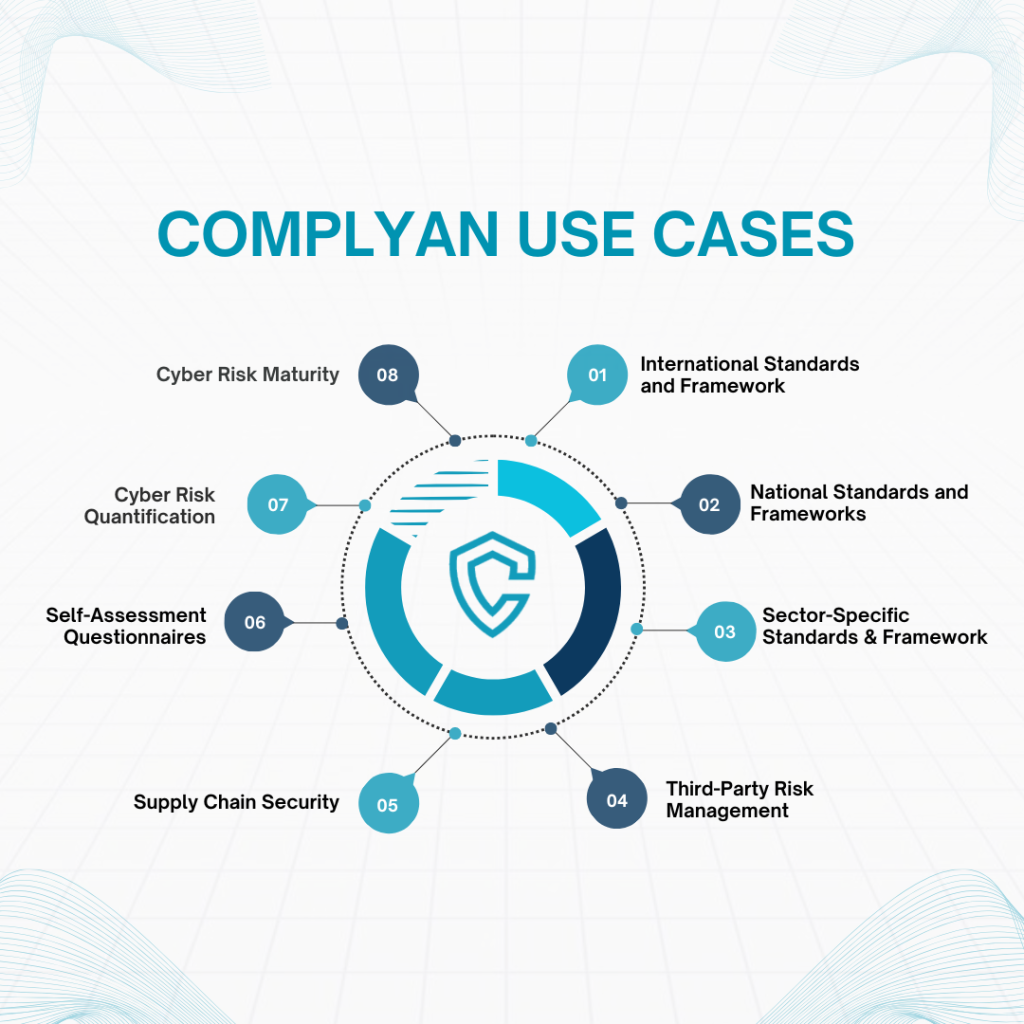
Complyan is designed specifically for this challenge. Complyan consolidates compliance management, risk tracking, audit preparation, and policy governance in a single environment. For organizations in the Middle East dealing with overlapping regional frameworks alongside international standards, the platform maps controls across requirements, so a single implemented control can satisfy multiple frameworks simultaneously, reducing duplication and making audit evidence collection continuous rather than reactive.
Complyan also supports third-party risk management, executive and board reporting, cyber maturity assessments, and data privacy compliance, giving compliance programs the breadth they need as regulatory obligations grow in scope.
Compliance Mapping: Working Across Multiple Frameworks
Organizations that operate across industries or geographies frequently find themselves managing obligations under several frameworks at once. Manually tracking requirements for GDPR, PCI DSS, and ISO 27001 simultaneously creates duplication and confusion.
Compliance mapping solves this by identifying overlapping controls across frameworks. A single access control policy, for example, may satisfy requirements in GDPR, ISO 27001, and NIST CSF simultaneously. By mapping controls to multiple frameworks, organizations reduce the effort required to demonstrate compliance and identify gaps more efficiently.
This is particularly relevant for third-party risk management. Vendors and suppliers carry their own compliance obligations, and organizations are increasingly responsible for assessing whether their supply chain meets the same standards they’re held to. Frameworks like NIS2 make this explicit; supply chain security is no longer optional.
Building a Compliance Program That Holds Up
A compliance program needs several components working together to be effective.
Asset and data inventory. You can’t protect what you don’t know exists. A current inventory of systems, data types, and where sensitive information flows is the foundation for every other compliance activity.
Risk assessment. Compliance frameworks specify controls, but risk assessments determine which threats those controls need to address. Regular assessments keep the program grounded in actual business risk rather than abstract requirements.
Policies and procedures. Written policies give teams a reference point for expected behavior. They also provide documentation that auditors will look for, undocumented processes, however well-executed, don’t satisfy compliance requirements.
Training and awareness. Most security incidents involve a human element. Staff need to know what phishing looks like, how to handle sensitive data, and what to do when something goes wrong. Training is a compliance requirement under most frameworks, not just a best practice.
Incident response. A documented incident response plan, tested regularly, demonstrates that the organization can detect, contain, and report incidents within the timeframes regulators require. GDPR’s 72-hour breach notification window, for example, is nearly impossible to meet without a plan already in place.
Monitoring and audit readiness. Compliance evidence needs to be current. Logs, access reviews, vulnerability scans, and policy acknowledgments all need to be maintained and accessible when an audit arrives.
For organizations looking to manage all of this without building separate workflows for every framework, Complyan’s GRC platform consolidates compliance management, risk tracking, and audit preparation in one place, particularly useful for teams managing obligations across multiple regulatory requirements simultaneously.
Conclusion
Meeting the minimum requirements of a regulation keeps penalties at bay. It does not, on its own, build a resilient security program. Organizations that treat compliance as the destination tend to build programs that pass audits while remaining exposed to the threats no audit is designed to catch.
The security leaders who get this right use compliance as the foundation, then build beyond it. The goal is a program that satisfies any auditor, responds to any incident, and holds up under any board-level question about what controls are in place and whether they work.




 Governance and Policy Management
Governance and Policy Management