Control Mapping: The Smarter Way to Manage Multi-Framework Compliance
Most organizations don’t answer to a single standard. A healthcare organization operating in Abu Dhabi may simultaneously face ADHICS, ISO 27001, and the UAE PDPL. A financial institution in Saudi Arabia must satisfy both SAMA’s Cybersecurity Framework and NCA’s Essential Cybersecurity Controls, often while also maintaining an ISO 27001 certification. Each framework carries its own requirements, audit evidence standards, and documentation expectations.
Managing them in isolation is expensive and results in a fragmented compliance posture, with teams duplicating work without realizing it. Control mapping addresses this by linking internal security controls to the requirements of multiple frameworks, demonstrating that a single control can satisfy multiple obligations.
What is Control
A control is a specific safeguard, a policy/procedure, or a monitoring mechanism, put in place to manage risk and demonstrate compliance. Controls range from high-level management policies like data classification procedures to narrow technical implementations like enforcing multi-factor authentication on privileged accounts.
Every compliance framework breaks down into requirements, and every requirement needs at least one control to satisfy it. One well-designed control can often address requirements across several different frameworks simultaneously.
What Control Mapping Is
Control mapping is the process of aligning your existing control inventory with the requirements of one or more compliance frameworks and identifying where a single control addresses obligations across multiple standards. The output is a structured matrix showing, for every control you operate, which framework requirements it satisfies fully, partially, or with gaps that require remediation.
This works because frameworks like NCA ECC, SAMA CSF, ISO 27001, NIST CSF, and PCI DSS were all built to address overlapping security challenges. A vendor risk assessment process can satisfy requirements across SOC 2, ISO 27001, and GDPR at the same time. Control mapping makes that overlap visible, and auditable, rather than leaving it buried across disconnected compliance workstreams.
Why Organizations Skip It, and Pay the Price
Without a mapped control structure, compliance teams run parallel tracks: separate evidence collection, separate documentation, and separate testing cycles for each framework. The same audit request gets answered multiple times with different versions of the same document. Teams burn time, auditors encounter inconsistencies, and coverage gaps only surface during formal assessments when it’s too late to address them efficiently.
This is a visibility problem. When controls aren’t connected to requirements systematically, there’s no reliable mechanism to confirm whether existing controls satisfy a new regulatory obligation, or whether a system change just invalidated several mapped requirements. The audit becomes a discovery process rather than a verification process, which inverts the entire purpose of compliance readiness.
How to Build a Control Mapping Program
- Create a unified control inventory by gathering all controls from different departments, including technical, procedural, and administrative areas. Standardize descriptions, eliminate duplicates, and assign each control a unique ID. Organize controls into categories such as access management, incident response, data protection, and vendor oversight.
- Decompose framework requirements into measurable statements. Broad clauses map poorly. Instead of aligning an access control policy to an entire ISO 27001 section, break the requirement into discrete elements: user provisioning, access reviews, privilege management, and MFA enforcement. Granular decomposition produces defensible, precise mappings.
- Map controls across frameworks using a matrix. A control may fully satisfy a requirement in one framework, partially satisfy it in another, and need enhancement to meet a third. Document coverage levels explicitly.
4. Identify and address gaps. Mapping naturally exposes weaknesses: requirements with no supporting control, controls that exist but aren’t documented, and coverage that depends on a team unaware they hold accountability for it. - Assign ownership and set review cycles. Control mapping requires ongoing maintenance. Business changes, system updates, and framework revisions all affect existing mappings. Quarterly reviews tied to audit cycles keep the structure accurate and defensible.
The GCC Compliance Reality
Organizations operating across the Gulf Cooperation Council face one of the most complex multi-framework environments in the world. Each country enforces cybersecurity through distinct regulatory requirements. Saudi Arabia’s NCA ECC 2:2024 defines 114 controls across 29 sub-domains, with compliance tied directly to national security obligations. SAMA’s Cybersecurity Framework requires financial institutions to formally document any control deviation as a risk acceptance, a legal instrument reviewed directly by the regulator.
The UAE’s Information Assurance Standard imposes 200 controls across 12 domains, with mandatory annual recertification and penalties up to AED 5 million. Dubai’s ISR, Abu Dhabi’s ADHICS for the healthcare sector, and Kuwait’s CBK requirements all layer sector-specific obligations on top of these national mandates.
Managing these separately is neither practical nor efficient. The organizations that handle this well identify structural overlaps between frameworks , for example, the functional alignment between NIST CSF’s five core functions and Bahrain’s CBB Cybersecurity Framework, and build a unified control set that addresses the most stringent requirements across all applicable standards. Structured control mapping is what makes that approach operationally viable.
How Complyan Supports Control Mapping
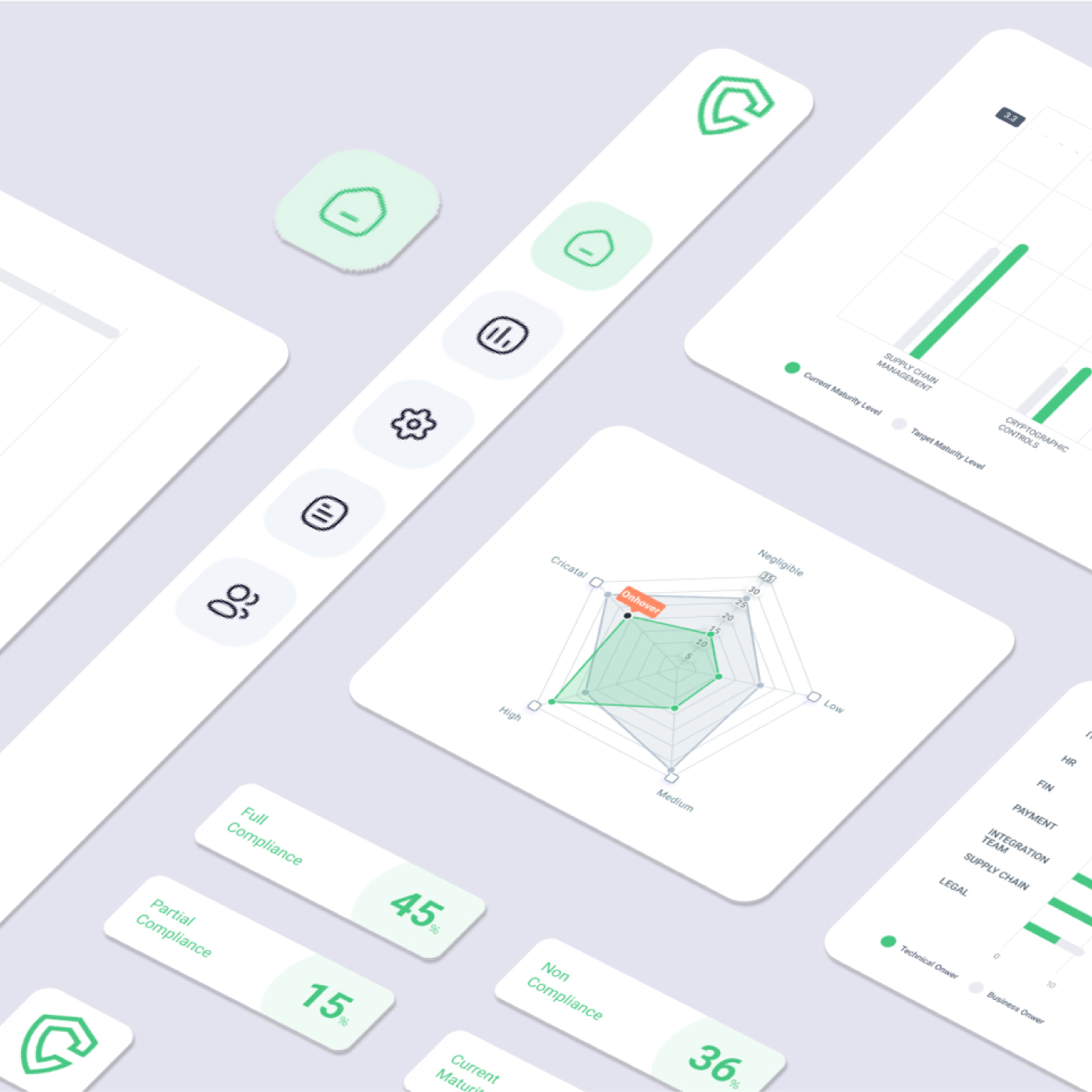
For organizations managing compliance across multiple frameworks, Complyan provides a centralized GRC platform that includes control mapping as a core capability. Complyan uses a proprietary matching engine, developed by analyzing existing industry mappings and control framework documentation, to align controls across international and regional standards within a single system of record.
The Complyan framework marketplace covers GCC-specific standards including UAE IA, Dubai ISR, ADHICS, UAE PDPL, NCA Saudi Arabia, SAMA, and CBK, alongside international frameworks, including ISO 27001, NIST CSF, PCI DSS, SWIFT, GDPR, and ISA/IEC 62443. Organizations operating across multiple GCC jurisdictions can benchmark and map controls across all applicable frameworks from one platform, rather than managing separate documentation and evidence trails for each.
Cross-framework mapping within Complyan eliminates redundant testing by showing precisely how a control already validated against one framework satisfies the requirements of others. Role-based access controls allow different stakeholders, CISOs, compliance officers, auditors, and risk officers, to access the compliance data relevant to their function, with full drill-down into control coverage and gap status.
For organizations building a structured cyber risk management function, Complyan connects control performance directly to risk registers. Risks are assigned owners, tracked through treatment cycles, and monitored with automated alerts, closing the gap between compliance posture and actual risk exposure that manual approaches consistently leave open.
Conclusion
Control mapping changes compliance from a framework-by-framework exercise into a structured program where effort compounds rather than duplicates. The organizations that do it well audit faster, spend less time on evidence collection, and carry a far clearer picture of where actual coverage gaps exist. For organizations in the GCC managing overlapping national and international obligations, a purpose-built platform that handles cross-framework mapping isn’t a convenience; it’s what makes the compliance program maintainable as regulatory expectations continue to rise.




 Governance and Policy Management
Governance and Policy Management